Recent posts
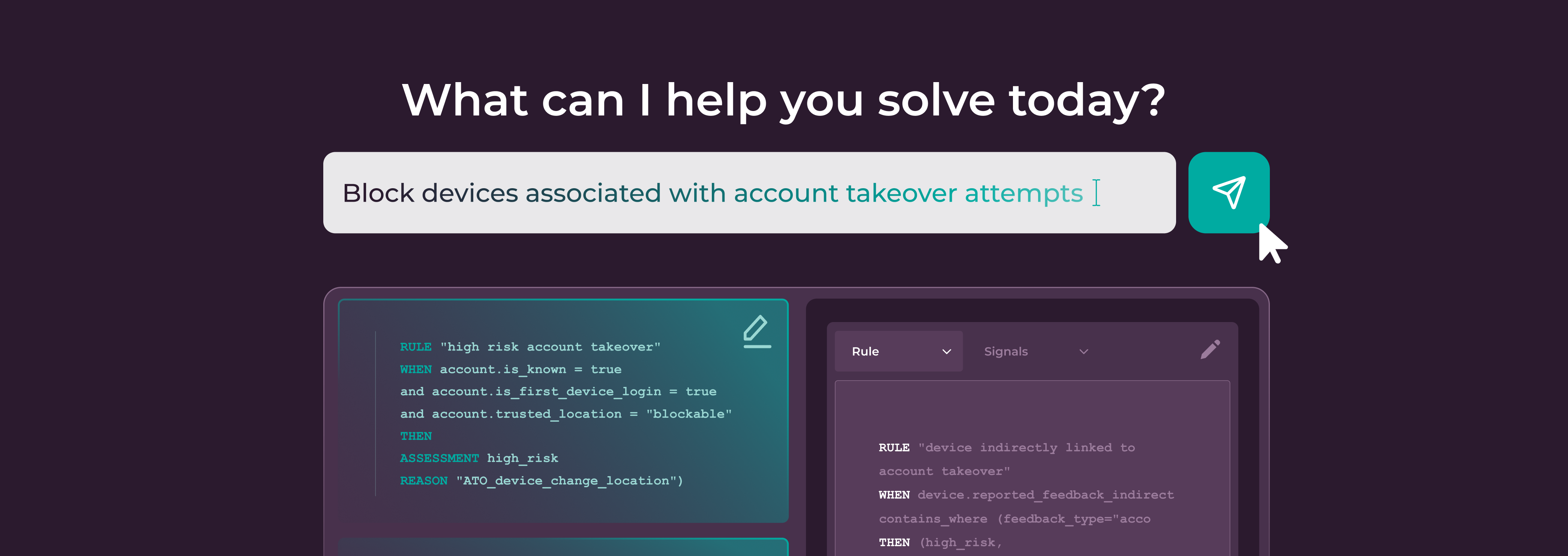
AI Policy Editor: The Next Innovation in How Fraud Rules Get Built
Discover how Incognia's AI-powered Browser ID redefines web...
Why Incognia’s AI-Powered Browser ID is the Next Standard for Web Identity
Discover how Incognia's AI-powered Browser ID redefines web...

Incognia’s Network Graph: Persistent Device ID for Faster Fraud Investigations
Persistent and tamper-resistant device IDs in Incognia's...

How Marketplaces Can Outsmart Seller Fraud in 2026
Discover how to combat sophisticated seller fraud in 2026...

Episode 4: How Rapido Balances Driver Supply with Fighting Fraud
Learn how Rapido balances driver supply and fraud...

How App Cloners are Becoming a One-Stop-Shop for Fraudsters
Take a deep dive into the rise of app cloners and what...
