-
Reduza roubos de contas
-
Reduza fricção
-
Reduza fraudes

No mundo de hoje, os usuários de dispositivos mobile trocam muitas vezes de aparelho, porque estão atualizando ou substituindo um dispositivo perdido ou roubado. A fraude do SIM Swap aproveita esta dinâmica para iniciar mudanças não autorizadas de dispositivo com a intenção de roubar contas.
Garantir a integridade do dispositivo é o primeiro passo na prevenção de fraudes mobile. Ao mesmo tempo, os usuários também querem um método fácil para trocar seu dispositivo, que lhes permita recuperar suas contas rapidamente.
A Incognia funciona silenciosamente em segundo plano quando um usuário tenta fazer login com um novo dispositivo, verificando sua localização exata e comparando-a com seu comportamento histórico. Se houver correspondência, uma pontuação de baixo risco é entregue. Se não houver correspondência, é entregue uma pontuação de risco elevada. Todos os processos acontecem em segundo plano, sem acrescentar nenhuma fricção para o usuário.
O usuário digita as credenciais de login.
A Incognia verifica se o dispositivo do usuário está sendo emulado ou falsificado e fornece uma pontuação de risco.
A Incognia compara a localização atual do usuário com seu histórico de comportamento de localização para avaliar e entregar uma pontuação de risco.
Visualize os detalhes sobre as avaliações de risco e acesse suas evidências associadas.

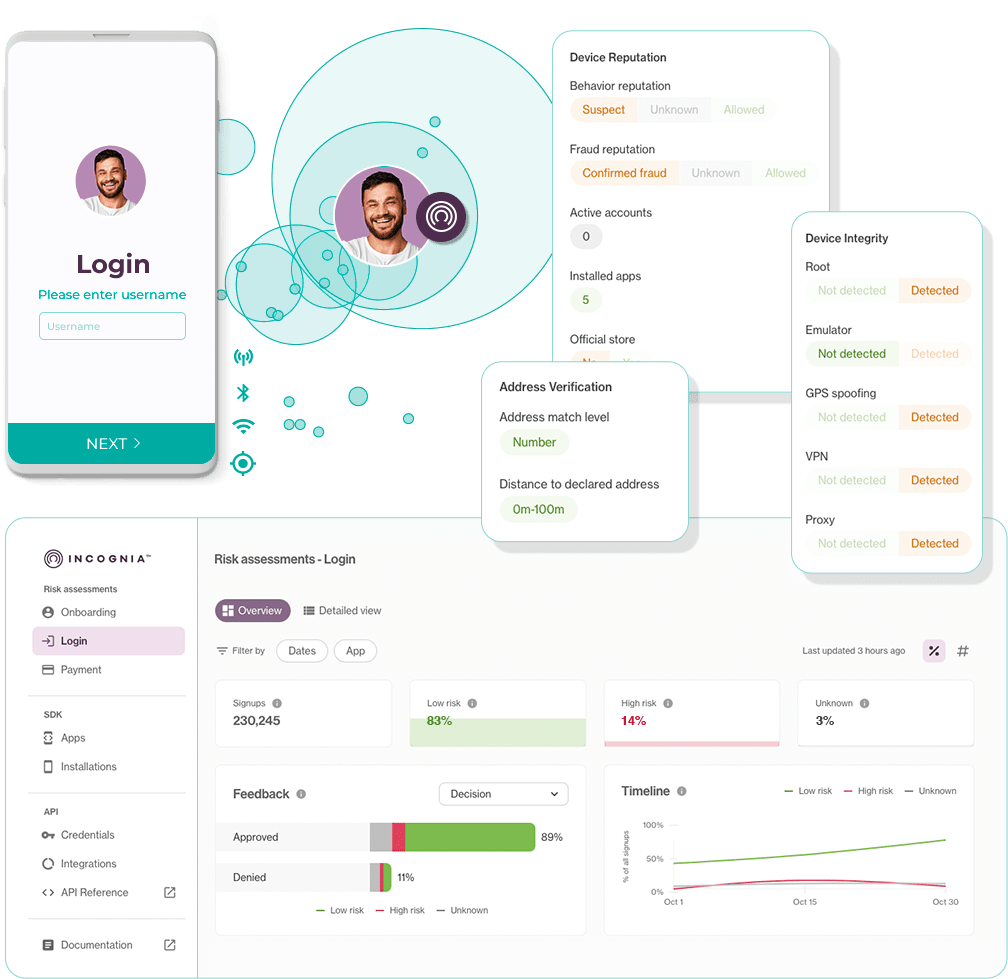
Fornecemos um SDK mobile leve e APIs intuitivas para facilitar a adição de localização e inteligência do dispositivo às avaliações de risco durante toda a jornada do usuário.
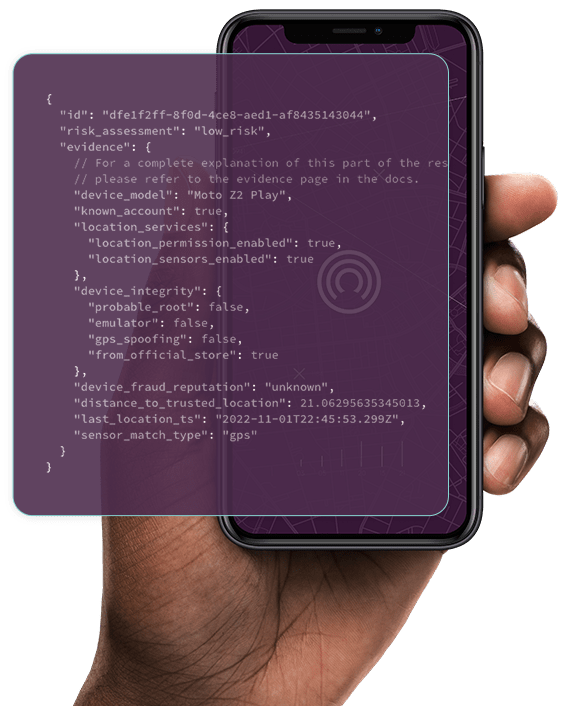
Trabalhe com respostas de API bem estruturadas e fáceis de entender
Suporte técnico através de:
By clicking "Accept" or continuing to use this Website after this notice, you agree to our Terms of Use - including your rights, responsibilities, and how we handle disputes.