Recent posts

Behind Eight Launches in Eight Weeks
Discover how Incognia's rapid eight product launches...

Web Sessions Now Have a Location Signal Worth Acting On with Trusted Location
Discover how Trusted Location for Web empowers fraud teams...

Introducing Location 2FA: The Second Factor That Can't Be Phished
Discover Location 2FA, a revolutionary second factor...

Proving You're Human Shouldn't Require an Eyeball Scanner
Discover a revolutionary approach to proving humanity...
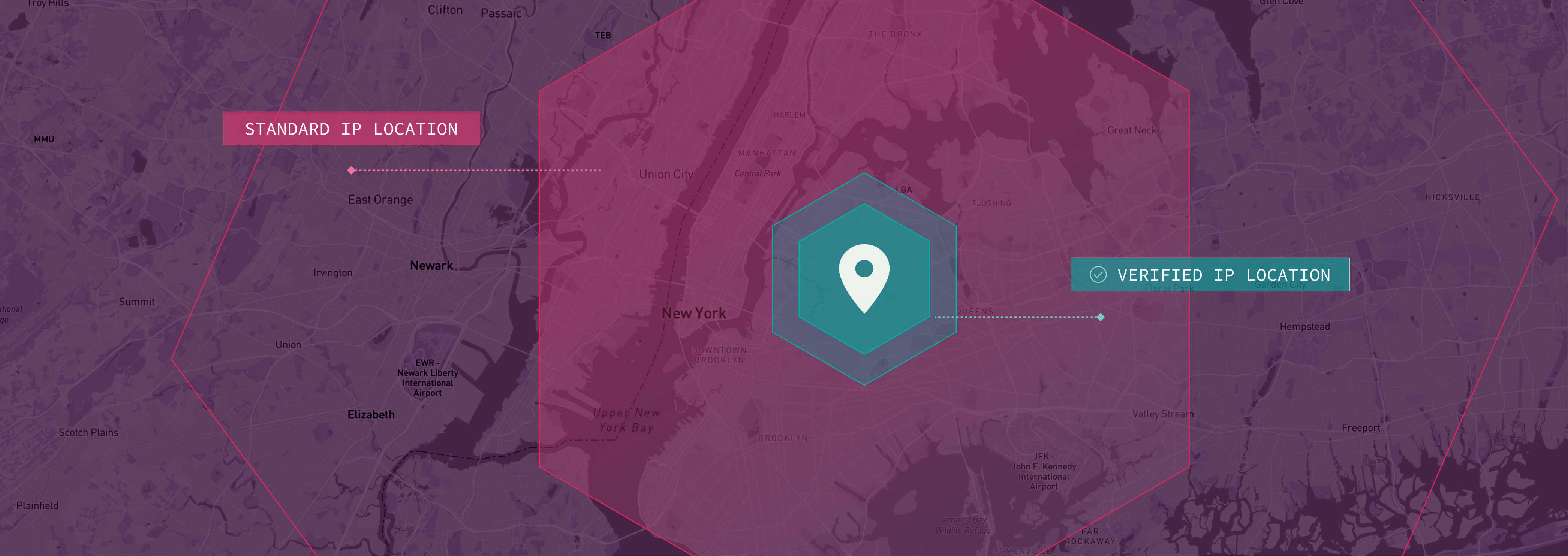
Verified IP Location: Know Where Your Web Traffic is Actually Coming From
Enhance security with Incognia's Cross Device...

Cross Device Authentication: Verify the Right Person in the Right Place
Enhance security with Incognia's Cross Device...
