- Blog
- Account Takeover Prevention Using Location Behavior
Account Takeover Prevention Using Location Behavior
90% of legitimate logins happen at Trusted Locations, making location the strongest trust signal on mobile
Subscribe to the Incognia Newsletter
With the rapid increase in the use of mobile apps, more people than ever are managing their finances, paying bills, and shopping from their mobile devices. The reason is simple; it’s just more convenient. But as more transactions originate on mobile, the channel has become a bigger target for account takeover attacks. While many existing technologies help reduce the threat of account takeovers (ATOs), fraudsters continue to employ new techniques and ATO on mobile is a growing problem.
But there is good news for mobile users. Location behavior gathered from sensors on mobile phones is now being leveraged to significantly mitigate ATO attacks on mobile, by identifying the locations that are "trusted" for each user.
Each user's location behavior pattern is unique, and using this information provides the strongest trust signal on mobile.
How does it work?
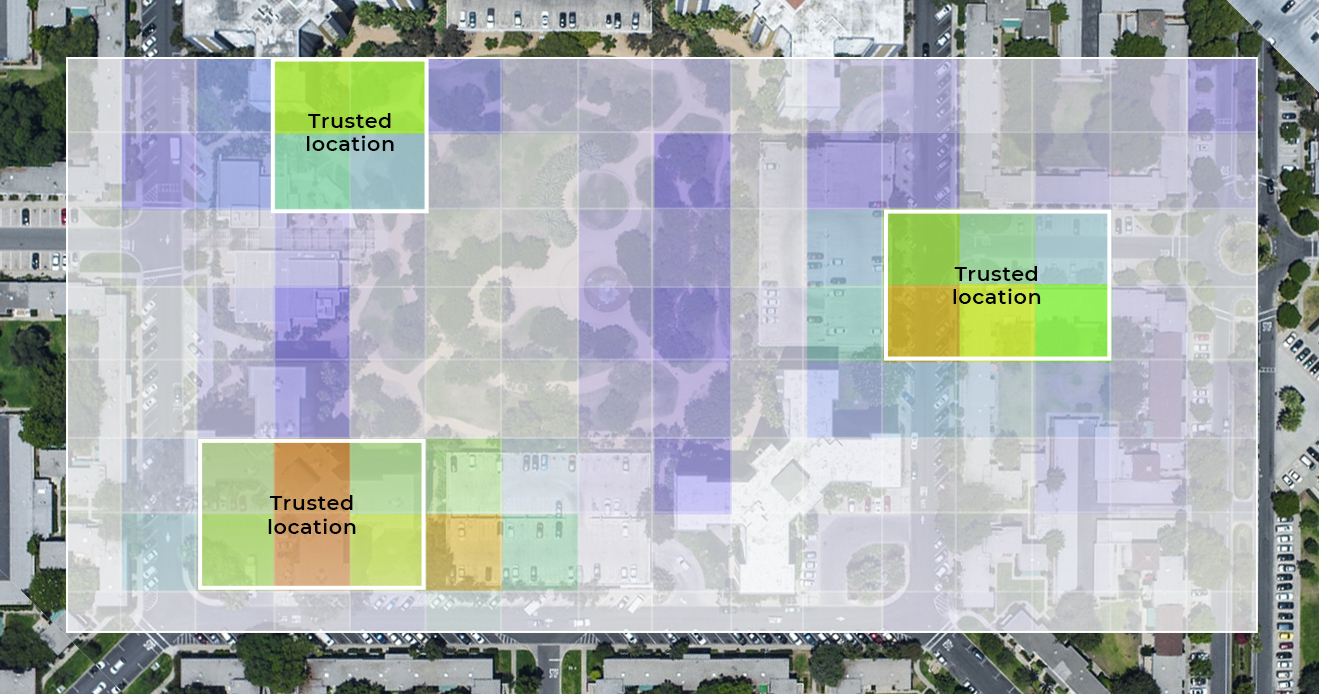
Incognia's location technology works in the background, silently building a user’s unique location behavioral profile, without linking to any other piece of personally identifiable information (PII). As it collects data, the Incognia platform learns which locations are trusted for each user and assigns context to them, like home or work. This location profile enables Incognia to provide highly accurate risk assessments based on location, including differentiating legitimate travel or device changes from an account takeover.
[banner_1]
What makes this different?
Location offers a level of resolution and continuity that enables a higher degree of anomaly detection, resulting in better account takeover prevention for mobile. These anomalies include inconsistent velocity patterns or radical changes of location behavior. Best of all, this approach not only protects mobile accounts, but it reduces unnecessary friction for legitimate users.
Location information is one piece of data that fraudsters always conceal or spoof.
The results speak for themselves. Analyzing tens of millions of devices, Incognia has found that the majority of mobile logins, sensitive transactions, and purchases occur at Trusted Locations and there is a close correlation between mobile transactions initiated at a trusted location and low risk.
This shows that evaluating whether a user is at a Trusted Location is an extremely precise way of measuring risk at login. For 90% of the cases, the friction created by passwords and MFA can be removed as for 10% of the cases, fraudulent activity can be more easily spotted. In fact, we routinely see false-negative rates below 0.004% and a reduction of over 85% of account takeover attacks.
Fraudsters are continually retooling and evolving their techniques and location intelligence is helping companies stay ahead of the game. Additionally, Incognia's fast-growing mobile network, including tens of millions of devices, creates a consortium of fraud data, enabling companies across verticals to work together to defeat fraud.
It's a never-ending battle against fraud, but Incognia has your back.
To learn more about account takeover prevention using Incognia read more here>>