- Blog
- Recognize New Mobile Devices for Less Fraud and Friction
Recognize New Mobile Devices for Less Fraud and Friction
In a world where a frictionless UX is just as important as a secure account, learn how to leverage behavioral data to gauge the risk of SIM Swap fraud.
Subscribe to the Incognia Newsletter
It can be a real pain to regain access to banking and shopping accounts on a new device after a smartphone has been lost or stolen. Without a device ID, SIM card3' or backup codes from an authenticator app to verify identity, it can take several days until the account owner is finally let back into their mobile accounts. Perhaps this wasn’t such a big deal in the past, but in 2020 it became a health and safety issue. Being locked out of both an online and mobile banking account in the middle of a pandemic, when physical branches are closed and customer service hours are limited, becomes a bigger problem.
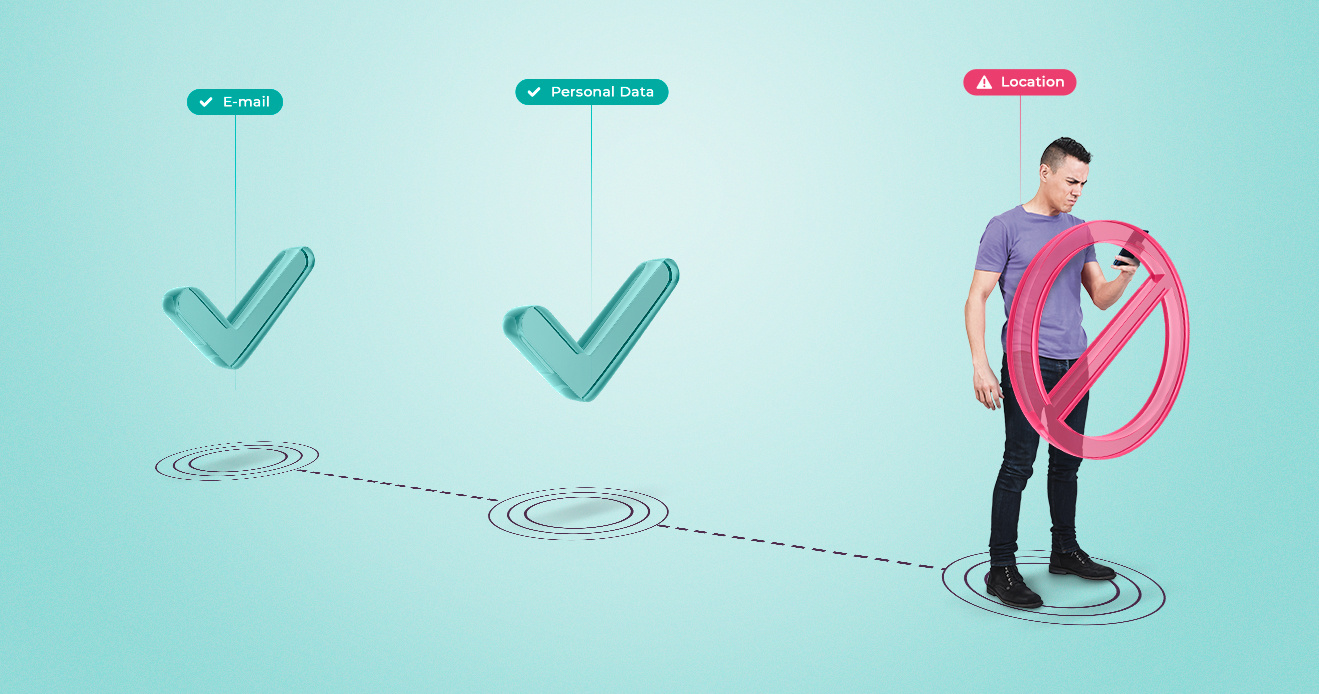
While most of the time security measures may feel like a nuisance to users, they are put in place for good reason. In the case of registering a new device, security is high for the user's protection. SIM swap attacks are an aggressive form of account takeover fraud, designed to mimic a user that has lost their phone. It starts when a fraudster obtains personal information, either by phishing or by purchasing it on the Dark Web. They then contact the mobile user’s telecom provider and switch their number to the SIM card on the fraudster's phone. This enables them to intercept other forms of identity verification in order to gain access to digital accounts, like email, which is then used to take over banking or other mobile commerce apps enabling them to commit financial fraud.
While additional mobile security is warranted, the added friction it creates makes it inconvenient for legitimate users.
Friction is counterproductive in the fight against fraud as many users choose not to implement solutions that introduce too much of it.
While 53% of the US population has embraced the good with the bad, swallowing the friction that one-time passwords (OTP) produce in exchange for the peace of mind that strong account security brings, just under 50% of the population isn’t willing to put up with the daily inconvenience. They opt instead to take their chances with fraud.
But there is a better way to balance fraud and friction in order to keep legitimate users both secure and satisfied with their mobile experience. Layering risk scores to create a dynamic fraud decisioning process can give organizations more control, trigger step-up authentication when risk is present, or remove friction when the returned risk score is low. Passwordless security solutions, like behavioral biometrics, are a great addition to a multi-tiered approach. They can analyze behavior in the background to silently identify if step-up authentication is necessary.
Let’s take the SIM swap example:
Behavioral biometric solutions are able to tell if a new, unfamiliar device is logging into an account from a familiar location or miles away from any previously visited location.
In the case of a legitimate replacement device, the app would be able to recognize that the login was coming from a new device that is in a familiar location, where previous logins were recorded. This way the app can infer that the legitimate owner of that account is logging in from a new device without introducing any unnecessary friction.
What this shows us is that more security is not always better for mobile. Before imposing maximum security on users, companies should leverage behavioral data to gauge risk. In a world where a frictionless UX is just as important as a secure account, behavioral risk scores can help balance the scale. Learn more about Incognia’s Zero‑Factor Authentication solution.