Passwords are a problem for security because they can be easily stolen, guessed, or cracked through various means.
Human-generated passwords are often weak, making them susceptible to brute-force attacks. In a brute force attack, a cybercriminal uses a program to try passwords manually; brute force programs can try anywhere from 10,000 to one billion password guesses per second.
Unfortunately, passwords that are easy for users to remember are also easy for hackers to guess. Weak, common passwords like “123456,” “password123,” or those using keyboard patterns like “qwerty” can be cracked in as little as a few seconds.
Users often reuse the same password across multiple accounts, making a single password breach potentially disastrous. A criminal who gains access to leaked credentials for one website can use a credential-stuffing program to automatically try those credentials against hundreds of other sites, including online banking portals.
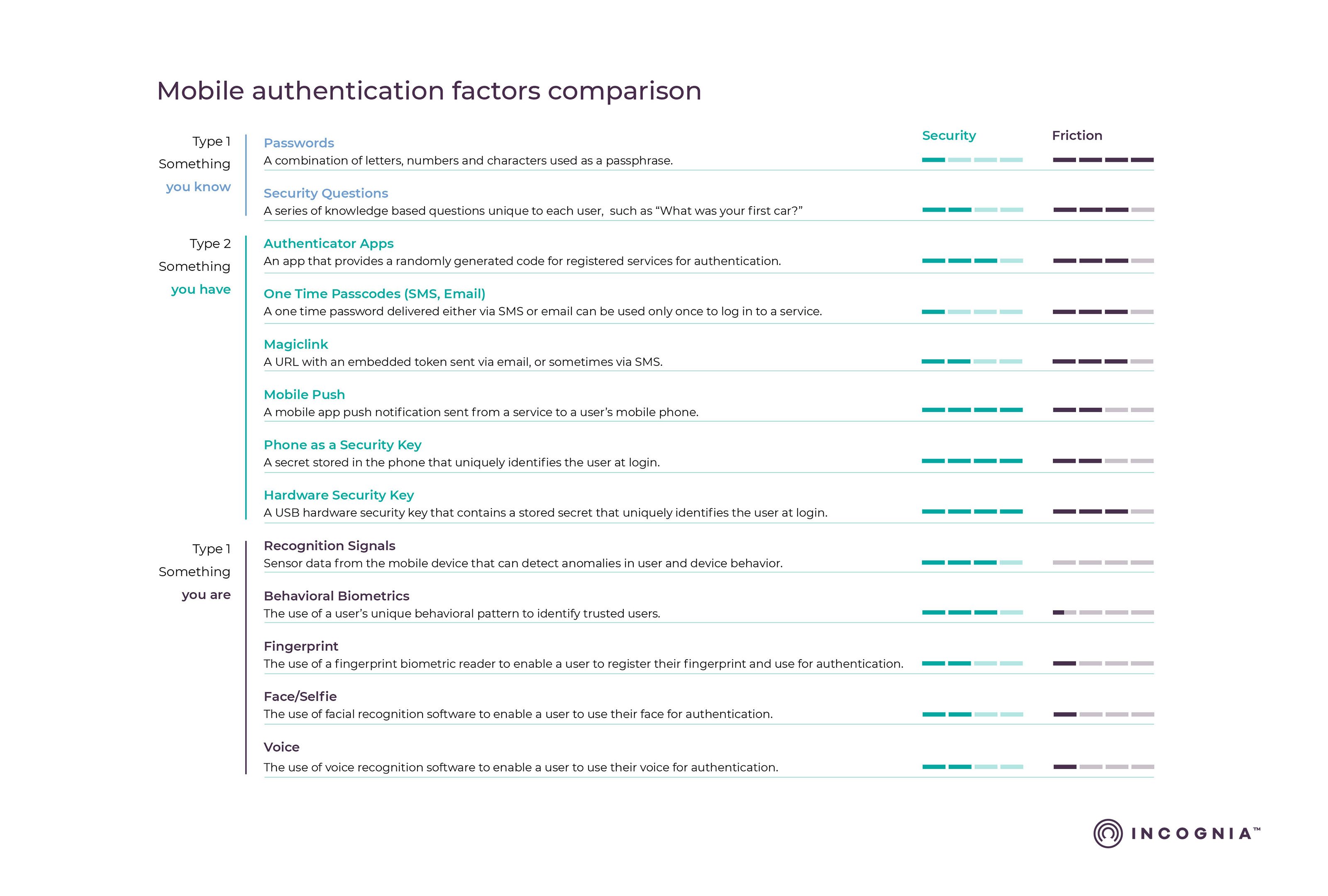
Furthermore, the centralized storage of database passwords creates a single point of failure that can result in large-scale data breaches. To address these issues, NIST recommends using strong passwords and long passphrases and employing additional account security measures such as two-factor authentication. However, while these measures increase security, they can also increase consumer frustration with the authentication process.