- Blog
- Real-Time Fraud Prevention in the Age of Faster Payments
Real-Time Fraud Prevention in the Age of Faster Payments
In the fast-paced world of digital transactions, faster payment rails are revolutionizing the financial landscape. But along with this ease and speed come new fraud risks. Incognia’s recent webinar delved into the growth of faster payments, what financial institutions are doing to defend against faster payments fraud, and what other tactics can help safeguard against the associated fraud risks.
Subscribe to Incognia’s content
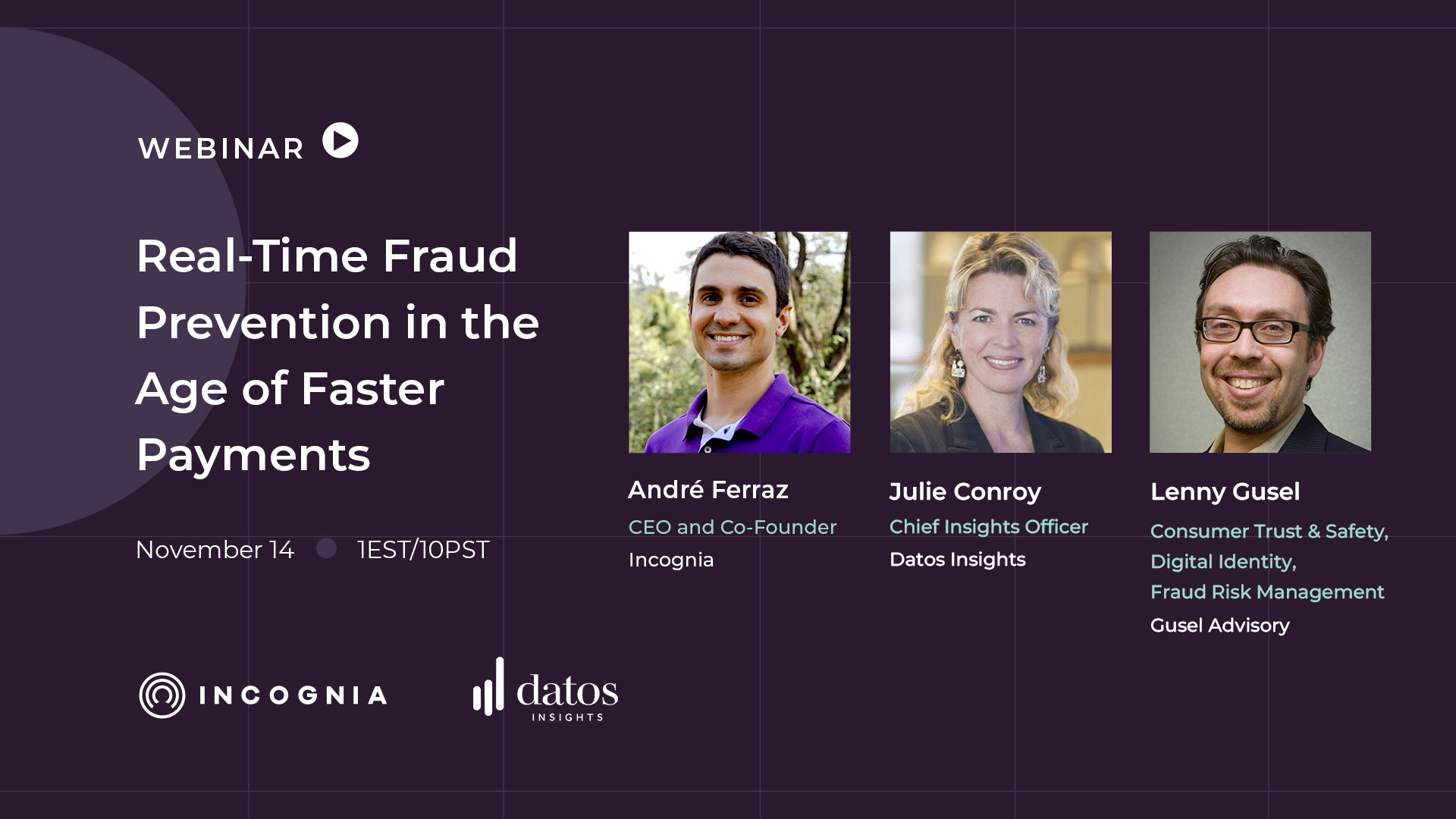
In the rapidly evolving landscape of real-time payments (RTP), financial institutions worldwide are grappling with the mounting challenge of fraud prevention. Incognia’s recent webinar featuring André Ferraz of Incognia, Julie Conroy of Datos Insights, and Lenny Gusel of Gusel Advisory offered an in-depth exploration of this critical topic.
In this recap, we’ll delve into the important topics discussed by the speakers, including the increasing global adoption of faster payments systems, the intricacies of authorized vs unauthorized fraud in this area, and potential fraud prevention solutions for faster payments (focusing particularly on location intelligence).
Key TakeAways
- Faster payment rails are coming, and with them, fraud problems are only going to get worse unless stakeholders intervene
- If fight back against fraud is going to back, better mule detection has to happen first—mule account enable fraud and scams by letting fraudsters reap their gains without getting caught
- This is every financial institution’s fight—no one is excluded. That means there’s tremendous possibility for collaboration between FIs
Real time payments and faster payment rails are here to stay
Wherever faster payment rails get introduced, they tend to catch on and gain popularity quickly. The panelists discussed a few different countries that either currently use RTP systems or will be soon.
The UK emerged as an early adopter, launching its initial set of faster payment rails back in 2008. In the US, the landscape differs with multiple faster payment rails, including Zelle and RTP. The July 2022 launch of FedNow further expanded the US faster payment ecosystem.
Pix, Brazil's RTP innovation, launched in November 2020, swiftly gaining traction. Within a year, Pix volume surpassed card payment volume in the Brazilian market. André shared insights on Pix's impact, highlighting how its fee-free structure transformed the market. He shared that when he visited Brazil a year after Pix’s release, he witnessed the rapid transformation that had taken place, evident in how people used Pix for even the most informal transactions (including buying coconut water on the beach).
It’s clear through the rapid and increasing adoption of these systems that they’re here to stay, and that means finding a way to address adjacent fraud concerns sooner than later.
Authorized vs unauthorized fraud and the question of shifting liabilities
As Julie pointed out, there are two types of fraud when it comes to real-time payments. The first is authorized fraud, commonly known as scams. In this case, the customer is using their own account to send their own money, but they’ve been tricked or socially engineered into doing so by a fraudster. In unauthorized fraud, the fraudster is the one sending the money without the account holder’s permission, typically after an account takeover.
Typically, unauthorized fraud has been the financial institution’s responsibility, while consumers are liable for authorized fraud. As RTP becomes more widely adopted, however, regulators are reassessing whether this needs to change. In the UK, for example, liability for authorized fraud will be split between sending and receiving banks starting in October 2024.
Naturally, the possibility of being liable for authorized fraud has FIs paying extra close attention to their fraud prevention stacks, but because these scams involve consumers sending their own money from their own devices, they’re difficult to screen for. Adding to the complexity, Julie explained that Datos Insights research has shown that most consumers believe they would recognize a scam despite over a third of those same consumers admitting they’ve already fallen for one in the past.
So, a question emerges for the panelists: how do you prevent these types of fraud?
Location technology & other solutions for preventing RTP fraud
When the conversation turned to the best ways to prevent faster payments fraud and protect both FIs and their customers, the panelists brought up a few different ways that banks and other FIs are addressing increased fraud concerns.
Julie mentioned that two-thirds of the banks Datos surveyed in one study are likely to make major changes to their RTP control frameworks in the next year or two, with improving authentication factors being a significant area of focus. She also mentioned the need for better mule detection as a way to prevent the “scampocalypse” from growing further.
Lenny brought up the potential of machine learning models to quickly identify issues like mules and otherwise suspicious transactions. Following on Lenny’s comment, André added that quality data is critical to ensuring the efficacy of any ML model.
Lastly, André discussed how location technology can help fight faster payments fraud by helping identify new account creation more reliably as well as by acting as a secure authentication factor—most people, he pointed out, conduct sensitive transactions from trusted locations like their home or work.
As long as faster payment rails are around, fraudsters will try to take advantage of them. Among questions of shifting liability and regulation, it’s clear that FIs have an important responsibility to safeguard their customers against the growing risks of faster payments fraud.
For more information about fraud prevention in the faster payments age, you can find the full webinar recording here or read the transcript below.
David Nesbitt:
Hi, everybody. Welcome to this webinar, Real Time Fraud Prevention in the Age of Faster Payments. I'm David Nesbitt, Content Marketing Manager at Incognia, and I'll be your host for today's session. So thanks again for joining us.
We're excited to have you hear from our three expert speakers today. This is going to be a really insightful session, so I'm glad you're here. Hope you have your caffeinated beverage or beverage of choice. Tune in, get ready to really get some great learnings out of today's session.
So, as we're going through the webinar today, our speakers would love to hear what your questions are so they can make sure that you're getting the most out of our time together. So type questions or comments into the chat box as we go. We'll address some of those potentially as we go, or at the end in our Q&A time. So make sure to stick around for that. Hear what your colleagues are asking as they're watching as well.
Just a note in case you're wondering, to get ahead of any questions, we will be sending out the on demand video recording of the session to all registrants by email when it's available. So you can keep an eye out for that in the coming days. So next, let's look at the topics we're going to cover today in today's session.
So first, we'll talk about the landscape of faster payment rails. Then we'll look at the attack vectors FIs have to protect against with faster payments before we do a deep dive into how FIs are fighting these attack vectors today. So make sure you stick around to the end as well because we're finishing by digging into what else FIs really need to be doing to prepare and fill gaps in their fraud prevention strategy for faster payments.
And like I said earlier, we'll finish up with some Q&A. Look forward to hearing the questions and thoughts that you have. Before we jump into our content, let's learn a little bit about our speakers today. Andre, would you mind kicking us off by introducing yourself for the audience?
André Ferraz:
Hi everybody, I'm André Ferraz, CEO and co-founder at Incognia.
I have been working with geolocation technologies and device and security for over 10 years now. I'm excited to be here and to hear what Julia and Lenny have to share about real time payments as well.
Julie Conroy:
Great. And this is Julie Conroy. I'm the Chief Insights Officer at Datos Insights.
Many of you may formerly know us as Aite Novarica Group. I've been here for 13 years and like all of the advisors here, we all come from industry. So prior to my time leading the advisory team here at Datos, I managed the product management function at early warning services for many years. And prior to that, I was with a top 20 U.S. Credit card issuer managing a bunch of their payment processes and risk controls. I'll turn it over to Lenny.
Lenny Gusel:
Hi, everybody. My name is Lenny Gusel. Been doing strategic advisory for a while now, both with banking and operator side as well as with vendors to the fraud and financial crime industry.
And prior to that have held leadership roles running fraud and trust and safety teams to the likes of Robin Hood most recently, and before that spent a number of years at Chase building some of their platforms for fraud, identity, and authentication. And prior to that, Bank of America. Been in this space, for, gosh, almost 20 years.
Was actually in the UK when the UK converted to faster payments circa 2008. And I'm fascinated by all the things happening here in the United States and following some of the similar pattern parallels, and excited to be in this webinar with you guys.
David Nesbitt:
Thanks so much, Lenny. So without further ado, obviously we have a lot of great expertise here in the session. So let's get started with our content. And Julie, could you start us off by sharing some context about the landscape of faster payment rails today?
Julie Conroy:
Sure, so if we look at the next slide here, you know, we've been talking faster payments now for going on just over 15 years and the UK is so often on the vanguard of things related to payments, evolution, risk evolution that goes along with it.
So they launched their 1st set of faster payment rails back in 2008. You know, by 2021, fully 39 percent of all B2B UK payments were going over faster payment rails. By the end of the first quarter of this year, we saw that 1.1 billion payments in the UK were faster payments.
That represents a 16 percent year over year growth, so there continues to be this expansion of awareness, this expansion of use cases, this expansion of recognition that faster payments have a ton of utility for consumers and businesses. But, you know, unfortunately, the flip side of that is, it also has a ton of utility for fraudsters.
We did a study earlier this year—we're gonna be sharing a lot of data as we go along—where we interviewed banks across a number of geos, and among them are the flags that you see on the screen, the UK, India, the US, Brazil. This by no means is the faster payments universe. There's now over 60 countries that have embraced faster payment rails.
And yeah, as we'll talk about a little bit further along, you know, as fraudsters who recognize the opportunity for fraud across faster payments, and as they have really honed their attack vectors and their tactics in early adopter markets like the UK. We're seeing that they're doing this rinse and repeat across the geos and the banks and the consumers that subsequently adopt. India has seen great success with its faster payment rails.
It launched in 2016. By Q1 of 2022, the UPI enabled 64 percent of all ecommerce payments, which I think that's just an amazing statistic in such a very short period of time. And 31 percent of the payment volume, the US, you know, we've always got to do things a little bit differently here in the US and so we don't have one, but we have two faster payment rails, or three, if you count Zelle, but yes, as most people on this, this call probably now.
Zelle is really the consumer facing brand and the actual settlement behind the scenes happens either via ACH. Or via RTP Zelle and RTP rails both launched in 2017. And this year we've seen the official July launch of FedNow with well over a hundred banks going live in July on the FedNow rails.
As of 2022, we were seeing 2.3 billion Zelle payments a year. Same year we saw 1. 8 billion RTP payments representing 12 percent of US volume. And then I think Pix is a super interesting story and Andre is going to give us a lot of great color on Pix because he has a ton of expertise with those rails.
You know, they launched just in November of 2020, within 1 year. So, by November of 2021 Pix volume eclipsed card payment volume in the Brazilian market, you know, 2022, they saw 29.2 billion transactions. One of the brilliant things that the operator of Pix, the Brazilian central bank, did was, you know, November 2020, we were still in the middle of a pandemic and they started issuing stimulus payments across the Pix rails to consumers to generate immediate adoption.
They also created a mandate that any Brazilian bank with more than 500,000 accounts had to enable Pix. And so that's, those are two factors, and just the kind of rocket ship launch that we've seen of Pix adoption in Brazil.
Anything to add to this, Lenny or Andre, before we move on to the next slide?
André Ferraz:
Maybe I could comment shortly here about the Pix experience because it was right in the year that I was moving from Brazil to the US. So I moved in February of 2020 to start building Incognia, and it was interesting because what really changed when Pix was launched was not exactly the real time aspect of it, because we were already used to real time, almost real time payments for a long time.
Since I started banking, we had another system called TED that enabled payments that would settle in like three seconds. So it was near real time. But the difference here was that you had to pay conversion to US dollars. It was about like 3 to 4 per transaction so the adoption wasn't that high.
And one of the big changes that Pix brought to the market was they eliminated all the fees. It became free to send money instantly from one bank to the other. And that exploded very quickly. So I think one of the aspects that made the adoption also move very quickly was the fact that people were already used to seeing payments settle almost in real time.
So there wasn't a very significant change. It was basically the central bank coming to everybody and saying, “Hey, now this is free, you know,” and people started using it for everything. I didn't use it when it was launched because it was here and I was stuck because of the pandemic, I couldn't travel.
But I was shocked when I went back to Brazil to visit my family and I went to the beach and people were selling coconut water and saying, “Oh yeah, I'm not accepting cash anymore. Do you have a mobile phone so you can send me a Pix?” And I was like, “Wow, this really changed very quickly.”
I only spent like a year out of this country and it has completely transformed.
Julie Conroy:
That's fascinating. David, if we move on to the next slide, as I mentioned, you know, the U. S. does everything a little bit differently. And, you know, the latest entrance to the faster payment rails is FedNow. We're seeing as you look at the 100 plus banks that were in that 1st tranche in July.
It's financial institutions of all sizes. So if you look down the list—and it's a public list on the Federal Reserve site—it's small community banks and credit unions, regional banks, national banks. And so you've got this confluence of banks versus RTP, which tends to be a little bit more constant, concentrated at the larger banks in the US market.
If we look at the next slide, David, you know, we'll see that as you look at how fraudsters are capitalizing on the faster payments, faster fraud opportunity, which it's it's cliche, but it's true. There's 2 types of faster payment fraud. It's really important to differentiate that and we'll be doing that throughout this conversation because you've got authorized payments fraud, which is commonly known as scams, where the bank's genuine customer is socially engineered or duped into voluntarily sending money to the fraudsters account.
We also have unauthorized fraud, which typically manifests as account takeover. And the unauthorized is the fraud vector that we have been dealing with since digital banking began, it really became industrialized and a massive problem in the early 2010 decade and I think one of the reasons why authorized payment fraud or scams were still problematic and so top of mind for financial institutions.
This is among the top two questions that we get from our financial institution clients at Datos is, you know, what are best practices in dealing with authorized payment fraud. Because over the past 15 years, financial institutions have architected their digital channel fraud control framework around detecting that unauthorized activity.
And turning that on a 180 and determining what the intent behind your genuine consumer voluntarily sending money out of their own account is is really, really hard. And Lenny, I know you were instrumental in developing a lot of especially the unauthorized control framework. So I'd love to hear your perspective.
Lenny Gusel:
Yeah. What's fascinating to me is there's, as we've seen, faster payment rails going across the world. There were certainly a lot of folks who predicted that there was going to be a rise in authorized payment fraud. And the simple reason for that prediction was that the weakest link in all of our control frameworks and all of our systems are the human beings.
We saw a fairly rapid rise from back circuit to that back in 2008 when the UK converted to faster payments as an entire country, we saw a fairly rapid rise. And in this authorized payment fraud aware as Julie, as you were saying, we had 20, almost 30 years, across the globe to put in a lot of different controls and lots of different processes and policies, procedures and so on for how we were going to dealing with people's accounts, online accounts, online credentials being taken over and bad guys getting into our online banking accounts and sending money.
Watching the actual response of fraudsters and how quickly they have taken advantage of faster payments using that weakest link, the human being and effectively duping, you know, tricking, scamming people into sending money in all kinds of ways is amazing to see the, how fast it is now, just to get a sense of it in the United States.
Again, we are still in the beginning stages of rolling out the actual real time settlement RTP and FedNow, but from the fraud perspective, Zelle has been a very enticing target as have other P2P rails been in the banking sector predominantly.
We are at a point already where about half, if not more of the payment, banking payment fraud in the United States is authorized as opposed to ATO unauthorized. If you look at the UK, my sense is from conversations I've been having, it's at 80%. And what's even more fascinating is that even in the unauthorized category, a large portion of that unauthorized, a bad guy figures out how to get your password and whatever other credentials get into your account. The last leg of that is people being convinced or duped into giving away their SMS codes or you know, sending the push notification on their mobile app.
It is a kind of a form of the customer doing it themselves, even in the unauthorized space. And so what we're dealing with, Julie, to your point of how do you actually discern who are the good guys and who are the bad guys? And then how do we deal with this entire ecosystem of payments being sent across institutions into bad accounts, which we're going to talk about, I know in the upcoming slides, and this entire ecosystem of fraud that has evolved given the faster payments rails is a real challenge.
Julie Conroy:
It absolutely is. And then you add liability to the mix, which, traditionally for unauthorized transactions that has been in most geos, North America's is no exception, that has been the bank's liability. Authorized historically has been customer liability. But we're seeing that shift rapidly and, you know, the UK once again on the forefront, you know, October 2024 for most forms of authorized payment fraud, it will be shared liability between the sending and receiving bank and all eyes around the UK globally.
And we're already seeing a number of jurisdictions contemplating following suit. Here in the US, there are a small subset of scam types, mostly bank impersonation types, with the set of circumstances where the bank now holds liability as of September of this year, and as we talked to Datos’s financial institution clients, they are already painfully starting to see that as we talk about authorized payment fraud or scams, one of the other challenges to an already challenging attack vector is that not all scams are created equal.
And so as you're kind of figuring out your detection strategies, as you're figuring out your talk off strategies to actually convince your customer not to send this payment, because they're being victimized. Yeah, there's so many different types and they have different timeframes. You know, you've got your grandparent scam where your grandson is in jail and you need to send bail money and it has to be now.
There's a lot of urgency. And the one commonality with all of these scams is they're really tapping into and pulling emotional levers. Unfortunately these scam rings are very good at doing this, you know, the dating scam, the romance scam. They're going for the long game.
It's kind of the other end of the spectrum from the grandparent scam, or it's a quick one. You're treating urgency, the dating scam, you know, you're engaging somebody over weeks, months to suck them in. Oftentimes it has a crypto investment component to it. So it's often known as pig butchering when it's got that component.
And as I talked to so many of our clients where they do detect some anomalous indicators, but then convincing this person that this person that they're emotionally invested in is actually a scammer is incredibly challenging to do. So that just adds to the further complexity of the scam ecosystem.
Lenny Gusel:
If I can jump in here.
What we need to understand is probably far and away the most difficult thing for financial institutions to deal with in this arena is, Julie, as you started saying, what is the treatment? So we can assume that there are going to be various ways of detecting that a payment is at risk of some kind of a scam without even necessarily knowing what kind, but then coming to an actual targeted and specific approach for how to treat it and what to actually do, how do you, as you said, Julie, how do you actually have that customer understand that they're being manipulated and that they should not send that payment?
Broadly speaking, I found it helpful for folks to think about this short term versus long term. Thank you. And that is very, very high level. And I think many financial institutions across the globe are starting to get very specific for potential types of scam and how to then do the treatment.
But the short term being, it's a kind of imposter or grandparent scam, or someone telling you that they're from the US or from the bank. I mean, you’re under immediate pressure to send something as opposed to the long term where you've had months and months and months of someone convincing you that you are in a deep relationship of some kind, whether it's an investment relationship, friendship or a romance scam, those are significantly more difficult to have the customer recognize what's going on.
And so broadly speaking, even just distinguishing between those two kind of long term and short term scams has been very, very helpful. But all of it gears towards how do we as an industry start to determine understanding not just intent, but understanding the background and the context of what is this payment about and why and how to communicate with the user in a real time scenario for trying to determine how to treat any particular payment at risk is possibly one of the most complicated things we need to do.
André Ferraz:
Absolutely. Another thing I would add here is that one of the complexities is that these things are happening off the platform. Right? They're communicating by text message, social media, phone calls, the financial institution doesn't have visibility into that, right? It only has visibility into who's logging in, which device is logging into this account, and who is it sending money to, right?
It's very hard to monitor what's going on behind the scenes because it could be a legitimate payment. Could be a real relationship, but it's very hard to observe what's going on behind the scenes. So that adds to the complexity of fighting this.
Julie Conroy:
Without question. And I love seeing in the UK market, in Australia, as we're looking at some of the emerging kinds of mechanisms that are being driven by the regulators in those countries that you have the social media platforms and the telecoms are being pulled into the mix because they are absolutely an instrumental part of this ecosystem. If we move to the next slide, I know we've got a lot to get through and we're almost halfway through already.
As we look at some of the research that we've done at Datos on this front, from the study that we did earlier this year, where we interviewed banks across US, UK, Canada, Brazil, and India. One of the questions we asked the financial institutions we spoke with was, you know, as you look at the trend associated with various types of payment fraud comparing 2022 attack vectors to those in 2021, you know, as you can see from this data, you know, those attack vectors leveraging real time payment rails are rapidly increasing and, you know, mule activity using real time payment rails is absolutely leading the way up for the majority of institutions, more than 10 percent for 57 percent of the institutions.
You know, we're also seeing that consumer ETO using real time payment rails is up for a huge chunk of institutions, 62%. And then as you look at, you know, things like the APP using real time payments again up for more than half of the institutions that we surveyed. And so that the faster payments, faster fraud adage really does hold true, unfortunately. As we go to the next slide, you know, we'll see that, you know, scam risk is really what's keeping people up at night.
This actually is data that we haven't even published yet. This is one of the first groups that's going to be seeing this data. But as we ask financial institutions, you know, thinking about your, your control framework and your financial institution's ability to adequately detect attacks and prevent losses.
What two types of fraud are you most concerned about this year? And as you can see here, by a significant margin, it is those consumer scam attacks. And I think it's that perfect storm that we see where, you know, fraudsters, the organized crime rings, they're doing the rinse and repeat.
They have a very well established set of attack vectors that they've tried. And really honed in the UK market. They're expanding globally. Our control frameworks are nascent. They're really not yet designed to adequately detect or prevent. And then you add the third leg of the storm, which is the liability shifts that we're seeing springing up or the threats of liability shifts.
I think that is why, you know, this is something that keeps people up at night. Lenny, Andre, anything to add to that?
Lenny Gusel:
I'm going to add a fourth leg to that, because it's the perfect storm, Julie, which is the operational complexity and cost associated with managing—there is such a huge operational overhead for how to deal with the act, those customer conversations, those treatments, both customers and frauds.
There's calling in to the call center in order to deal with all of those alerts and cases and so forth. How to tag them, how to mark them, how to resolve them. It is a big part of why everyone's up at night.
Julie Conroy:
You know, that is such a good point. And it's not just the customer facing operational aspect as I've talked to a bunch of our financial institution clients out in the U.S. market in just the 2 months since we've had that liability shift for a very small subset of cell transactions. They said that the operational overhead of just figuring out who has liability has been massively painful. And so it's the internal just liability assignment stuff as well that is taking tons of cycles.
Lenny Gusel:
Yeah, and on that, I'll say that it is probably kind of foreshadowing. I believe it's something that you have on slides coming up is how are sending and receiving institutions collaborating and sharing data in this entire environment in order to figure that out? And in order to actually then process and go through a set of prescribed policies, procedures and workflows for how they're actually going to do that.
It's a process. We're at the beginning of a couple of decades worth of making this work across our financial ecosystem.
Julie Conroy:
The collaboration piece, we'll speak to that a little bit. That's where I think we've got enormous untapped opportunity and we haven't even begun to scratch the surface there.
Unfortunately, David, if we move to the next slide, you know, I think the other massive challenge with scams is we've got a consumer population that think that they will know a scam if they see it. And we've got a couple of bits of consumer data. The piece that we put in here was just around education.
A number of institutions, as we'll see in future slides, one of the things they’re spending money on to combat scans is educating consumers and I think you could say that virtually every financial institution in North America is doing something to educate their consumers about scams. It's statement stuffers.
It's things on the mobile app. It is pop ups on the website. I know from my institutions, I get actually some pretty good emails, but I pay attention to them because I'm in the space, you know, as we survey consumers. And when we ask consumers, has your financial institution ever tried to educate you about scams?
As you can see from this chart, only one in four consumers think that their primary bank or credit union has tried to educate them about this, which shows that the challenge associated with consumer education is just trying to figure out how you can get it to sink in. Once again, I think the UK is a poster child for doing some stuff right on this front.
I just got back from London this morning, actually, and they have some really edgy and, you know, humor laden education campaigns that they put on the telly and they put in the tubes to really kind of break through and get consumers’ attention. I think in too many markets, we're still kind of seeing a white glove approach where you don't want to scare consumers and you know, it's very tentative and that's where one in four consumers really have even registered seeing it at this point.
The other bit of data from the same consumer survey was we asked consumers about, you know, if somebody tried to scam you, would you know it if you saw it? And like 75 to 80 percent of consumers were very confident they'd know it. But then later in the survey, as we'd asked if they had ever fallen for a scam, over one in three had fallen for one.
It shows cognitive dissonance there in the consumer base. David, if we move to the next slide, the other thing that I think is a work in progress in so many geos right now is just the policy for reimbursing scam victims. This particular data set came from a survey that we did in late 2022 where we asked about a firm's policy for reimbursing consumer scam victims.
And as you can see, there was quite a wide variety in terms of firms that reimburse very little, firms that take a case by case approach, firms that are reimbursing a good chunk of things. The two very interesting things about this data set for me were when we asked a similar question in a study that we did just a year prior to this one.
And at that time, at the end of 2021 in North America, very few firms, very few financial institutions were reimbursing for anything over 10 to 20 percent of consumer scams. And so you can see kind of the big jump we made in a year, and that was really when the Consumer Financial Protection Bureau in the US started making a lot of noise via guidelines via public statements about, you know, they were keeping an eye on this potential liability shifts and financial institutions started taking a second look at their policies.
The other thing, though, is you look at kind of just the selective process and you don't necessarily have a cookie cutter decision making process to determine who gets reimbursed and who doesn't. That actually plays into some of the regulatory jeopardy right there. Because if you're saying Lenny gets reimbursed, but Andre doesn't, you know, why is that?
Is that fair? Is that equitable? And so I think all of this is something that the ecosystems are grappling with, as we still have a lot of gray area in many geos about consumer reimbursement for scams.
Lenny Gusel:
And I'll say this is also one of the things that is feeding and fueling the rise in first party fraud. Reimbursement means money, and the fraudsters are very clearly aware of that.
I've heard estimates of the volume of reported fraud, reported scams, and how much they're rising. And don't quote me on these numbers, but it's 40, 50, 60, sometimes 80 percent in terms of an increase in volume, and in consumer reported fraud, the vast majority of that is consumer reported scams.
Again, the operational overhead of having to determine which of those are actually really good customers who have been scammed and which of them are first party fraudsters who are taking advantage of the liability shift and the entire reimbursement schemes that are being put in place.
Julie Conroy:
Yeah, absolutely. I mean, when the UK saw its first contingent liability shifts in 2019, where a good chunk of consumer scams got shifted to the FIs, you know, as my team and I talked to the heads of fraud at those banks, they immediately saw a spike in first party fraud and over the past 18 months to two years, we've seen a number of U.S. financial institutions publicly come out and say that they're going to start reimbursing bank impersonation scams overnight. They saw not only increases in first party fraud and bank impersonation scam claims, but you can also find YouTube videos out there that are training people as to what to say and how to do it.
The first party fraud piece of this is one that will absolutely jump as the liability shifts take place as well. David, let's keep us moving. Time’s ticking here, so I'm going to turn it over to Andre to share some more great insights from quick Pix in Brazil.
André Ferraz:
Yeah, so, here in this slide, basically, reinforces this point that the liability shifts have been driving behavior on how the financial institutions are reacting and reinforcing their controls. Right?
So, in this case here, for authorized attacks, right? What was interesting was that I saw that firsthand, in the beginning. In case of an authorized attack, the sending financial institution was reimbursing consumers, not because they were forced to, but because there was so much pressure from consumers because there was so much of that happening that basically people started talking about these issues in social media, et cetera, and the banks started to reimburse/
What happened after was that the central bank published that they were going to change the policy and they would shift liability towards the receiving FI. And suddenly our team starts receiving calls. “Hey, how can you help me detect new accounts?” Right? So it wasn't a problem. Like it was a problem, but it wasn't something that they were prioritizing at the moment until the central bank published that new resolution for this update on the policy, right?
It's really interesting to see what's going on in different markets. Because then you can predict where the FIs are going to prioritize their efforts in terms of building their stack. Right? So, for example, in this case, detecting new accounts became the top priority when that shifted.
Just one final comment on authorized attacks. Another thing that happened in Brazil was when Pix was launched, basically, what happened was everybody's smartphone became a wallet, but differently than the traditional concept we have for wallet, right?
Basically all the funds that the person had access to were available on that device. So that device actually has become extremely valuable. And what started happening was street criminals started targeting people that were actively using their smartphones. So the phone was unlocked and they were basically like riding a bike, stealing that phone, going somewhere near and basically making a Pix transaction, moving all the money that was available on that device, right?
Why was that? For example, many of the FIs in the beginning were relying on things like 2FA based on SMS, right? If you have the phone to that same device, right?
Be able to log into the account. And then transfer the funds right there with that device and everything looked fine because it was actually the same device that that user always used, et cetera. So, dealing with that was quite challenging. When the liability shifted and the receiving end became responsible things started moving in the right direction, and people started investing in the right things.
When it comes to the unauthorized attacks, this one is more straightforward, right? In this case, the FI reimburses them. So pretty much the same process we've seen since this existed, and then on the next slide, I think we get back to you, Julie.
Julie Conroy:
We'll start talking about some of the solutions set from here on out. So, not just the doom and gloom, but, you know, as we look at, you know, how institutions are fighting these factors, you know, we've seen real detection investments rise significantly since the pandemic. And I think if you're going to find a silver lining in a pandemic, then this is one good silver lining because, you know, we've been looking for a way to make a business case for meal detection for years.
You know, typically it's been challenging. Because the party that is detecting the mule activity is not the bank that's taking the losses. It's the bank upstream and it's the incoming bank that has the mules on its books. But with all of the stimulus fraud that we saw with massive increases in the population of mules, the concern over regulatory activity, again, the training of would-be mules on things like YouTube, the active recruitment of mules.
You know, there's a couple of stats in the sidebar that I'm not going to read through. These are from a Lloyd's survey of UK consumers about just the extent to which consumers have at least no vocal acknowledgement of doing things like being asked to move money through your bank account in exchange for a cut of the proceeds is something bad.
So this, you know, all points to this ballooning mule problem that we're now actively doing something about. So we did a survey where we looked at the extent to which FIs are increasing their investment in mule detection. And the great news here is that we saw that 64 percent of those that we surveyed are doing so, if we look at the next survey, and I'm going to move through these pretty quickly, just in the interest of time, we've got a lot of great content and dwindling time.
You know, I think on the unauthorized payment detection side, even though it's a more mature attack vector, we still see that a number of institutions see a lot of room for improvement. Yeah, as we asked about the confidence in their unauthorized or ATO control framework, only 43 percent of those that we surveyed really felt like they had had things in pretty good shape.
As we go to the next slide, you know, we'll see that the good news is you look at real time payments and that the evolution of the control framework, we do see that active change is coming. So, again, in the survey that we just closed out at the end of last month, we asked institutions how likely they are to make major changes, not minor tweaks to their real time payment control framework in the next year or 2.
As you can see here, um, 2/3rds of those institutions that we surveyed are likely to do so, which I think is just fantastic news. I'm going to the next slide. You know, there's, you know, especially in the ecosystem where we've been fighting this battle on an industrialized scale for 15 years. Yeah, the ATO ecosystem is much more mature than scams, but I do think that there's still considerable room for growth and evolution.
Yeah, as we asked about a whole variety of control factors that FIs are using, and I think you guys will all be able to get these slides after, so I'm not going to go through all of this, this eye chart, but if you look at just that bright green on the right side, those are controls that institutions, a good chunk of institutions don't even have deployed yet.
So I think, you know, the good news is even though there's still not 100 percent confidence among many FIs and their capability sets for ATO, there's a lot of tools at people's disposal that can help very effectively address it. David, if we go to the next slide here. Yeah, I think that the good news is authentication is getting a lot of focus as we look at those areas of transformation.
So as we ask financial institutions about where they are prioritizing their bets and their spend, digital identity, authentication controls are leading the way. And I will say, this is a survey that we have done every year for the past six years.
And authentication is in the top two every single year, which speaks to both the opportunities for improvements as we're looking at getting tired controls like KBA, which, you know, fortunately that one's almost dead. Um, but, you know, ubiquitous things like SMS OTP that are highly compromised, you know, working those things out of this out of the system and replacing them with things that not only are more effective from a security perspective.
But also can provide a better customer experience, which really is the win-win. David or Andre, Lenny, anything to add to that before we dive into this slide?
Lenny Gusel:
I would say what strikes me, and it's been striking me for quite a bit, and Julie, it's comes so clearly and as you're talking through the slides is how we're at a point as a result of all the transformation with real-time payments where every financial institution has to look across so many different aspects of their domain and really get to a level of maturity and professionalism, not just in your account takeover, not only in your scams and authorized fraud activity, not only in your mule account monitoring, but all of those together and across multiple touch points with their both consumers, small businesses, business banking.
And so we're really at a point where the level of kind of maturation and kind of professionalizing of where we've been plugging a number of holes, but with faster payments, every single financial institution is a position where they really need to look at how do they holistically invest across these different attack vectors in a way that continues to provide a reasonable experience and manages their liability and losses at the same time.
It's a lot of challenges all at once.
Julie Conroy:
Yeah, and you know, you and I were talking about this just earlier last week and doing all that and at the same time trying to provide a good and holistically uniform customer experience, you know, it's a pretty tall order. It's not easy to do.
Lenny Gusel:
It's a tall order and it's clear why authentication keeps popping up at the top because it's as much as much a question of how do you continue to give people a reasonable experience in the digital, as we've gone through digital transformation and as things continue to become more and more digital and how consumers interact, how do you give them a reasonable experience, one that's consistent, one that's easy, one that's safe and across all of these different channels.
So whether you're trying to fight ATO or not, you're still going to continue to make investments across your authentication identity landscape.
Julie Conroy:
Yep. Absolutely. David, if we can move over and, that's a great segue into just the business case as to, you know, as you are having to make the business case.
And unfortunately we still have to make business cases, whereas the bad guys just—and that's why this continues to be that lopsided chess game, where they're getting like three moves for every one we get at this point. You know, when we ask financial institutions, as they are driving change in their real time payment, real control ecosystem, as they are making investments in their fraud control framework, what are the key elements of the business case?
And I thought this was kind of interesting. Because we asked this question a lot as we're doing our various surveys of evolution of fraud controls here at DATOS. Typically, as we ask this question, customer experience is almost always at the top and usually closely followed by fraud losses. And, you know, it's only 10 points behind in this one.
But I did think it was interesting that we're feeling enough pain, both on the authorized and the unauthorized side of faster payment rails. That is, you ask executives about what is their primary driver of these business cases right now. It is those fraud losses that have that top slot. Andre, I know you talk to a lot of financial institutions, a lot of, you know, neo banks, cryptos, you know, are you hearing something similar on this front?
André Ferraz:
Absolutely. Yeah. If we observe the sales cycle, depending on the business case, it is completely different, right? So our solution addresses both the client experience. So it helps our customers provide a frictionless authentication experience, et cetera, but it also helps reduce fraud losses.
When the problem is fraud loss the sales cycle on our end tends to be at least half the time when compared to client experience. Right? Why is that? Well, basically the FI is losing money and more than that, they're seeing the problem scaling, right? Because if they don't fix it quickly, they become a bigger target.
Fraudsters collaborate a lot, right? So they communicate that if I have this vulnerability, let's attack them. So if they don't fix it quickly, it could become a much bigger problem. For sure, we see that fraud loss is the primary driver for the business case on adopting a new technology. It becomes a top priority more, more quickly.
Julie Conroy:
Absolutely. I know we've got some questions coming in. I want to make sure we leave time for this. Let's move on to the next slide here. So we at Datos run an impact award every year where we invite solution providers to submit the new innovations they released over the last couple of years.
We require that they be in production, that they have recommendations metrics that demonstrate the effectiveness of the solution, both from a detection as well as a performance as well as from a client experience perspective. And literally we get multiple dozens of submissions to this. The judging panel is—it’s truly an industry award.
So we've got a couple of judges internal to Datos that are on this. But we recruit a number of financial institution executives. They outnumber us three to one on the judging panel. And I'm pleased to say that Incognia got our winner of best digital identity verification innovation this year, as you look at some of the judges' comments as to why they were selected among the many submissions we got, it really was, you know, some of the client testimonials that we got.
This is a direct quote from one of the clients about the ability of the Incognia solution to lower false positives, reduce identity fraud, specific to, in this case, it was a new account creation, as well as an ATO use case. And it was the ability to do this with, you know, without invoking PII and having to go through some of those hurdles in the business case process.
And at the same time being pretty much passive and behind the scenes from a customer experience perspective. So congratulations to Incognia. Um, and Andre, I don't know if you want to add anything before we jump into some of our key takeaways and then open it up for questions.
André Ferraz:
Just like, thanks for that.
Really excited to see the recognition. I'd say the approach we decided to take here was actually very simple. We got back to the first principles and tried to understand, like, what is common among multiple online interactions we have and we realized that there were basically two things in common for all of those, which was for every online interaction—and it doesn't matter the platform, it doesn't matter if we are like in a metaverse or on a mobile channel or on a browser, on a desktop—we will always do that from a device and from a physical location. So we decided to go very deep on understanding these two things, understanding which device is this and where is it.
And by doing that really well, we found that we could create a more, let's say, universal solution for identity verification that would work across platforms and would fill some of the gaps that we have identified in the space, particularly when it comes to device intelligence, we noticed that fraudsters have developed many techniques to evade detection using device intelligence.
So we added this additional layer to fill those gaps, but very, very happy for the recognition.
Julie Conroy:
Absolutely. Well, well deserved. And if anybody on the webinar wants to see the full write up of the Incognia award and why they got it and the use cases, you know, you can reach out to the Incognia team and they'll be happy to provide you with a copy.
So, David, let's jump into our key takeaways here. And, you know, the scam problem is going to get worse before it gets better. Unfortunately we're still kind of on decline. We are definitely not even close to the downhill yet from a solutioning perspective. The good news I do see, though, is that with the monetary incentive that some of these liability shifts are taking, I think we're seeing the solution ecosystem accelerate probably faster than what we saw in the early 2010s as ATO became industrialized.
And we saw substantial motivation for FIs to spend there. I think we are seeing a number of really interesting solutions come to market that can help with these challenges on real time payment rails. Mule detection, I think it's, you know, that's the place where from an authorized payment fraud perspective, that's where the low hanging fruit lies because it's, it's easier to detect the anomalous behavior associated with a mule account than it is to try to figure out the intent behind your genuine customer sending an outbound payment.
And so that's where I think a lot of the solutioning we're seeing today are seeing success. And I think that's going to be some of our low hanging fruit from taking a bite out of this problem. You know, one of my colleagues has very aptly called it the scampocalypse.
And I think better mule detection is our way to really prevent it from achieving that scampocalypse status. And Lenny pointed out earlier, collaboration, both within FIs, across FIs, with the social media, the telecoms, that's going to be another key opportunity for us to get ahead of that curve. Turn it over to Lenny and Andre, and then I think, Andre, we've got one more slide, and we're getting close, so maybe, David, we just respond to questions by email after the fact.
Sounds great.
Lenny Gusel:
I'll just respond to one of the questions as part of a kind of reaction to this, to the slide. And there was a question in here around machine learning models and their effectiveness across these attack vectors. One of the things that I'm seeing a lot of financial institutions really focus on investment right now is how do they get much more facility with building their own to both building their own as well as acquiring machine learning models and having the kind of the technology stack that allows them to rapidly be able to deploy different types of machine learning models to address these problems so specific models for mule detection specific models for the sending side Specific models for the receiving side and the collaboration thereof.
They are absolutely a huge part of the equation. And I think a lot of investments from my perspective are being made. And how do I get some kind of facility with being able to rapidly or as rapidly as I can both be able to deploy them and take advantage of them and different kinds of models across the all three problems that are on the side?
André Ferraz:
Yeah. And to add to that on the machine learning front, like I'd say having high quality data is the most important thing here. Because if you don't have high quality data, it doesn't matter how good your ML model is, it won't perform. And in some cases, if you have access to very high quality data that, you know, it's not tempered and provides like good granularity in terms of understanding who's that person.
Sometimes when you have, again, very high quality data, rules sometimes perform better than machine learning models. So it all depends on the data. I would prioritize having access to the best data that you can and testing different models, testing rules as well.
It's not 1 or the other. In many cases, you use a combination of rules and sometimes rules for the most straightforward cases, ML for, like, the gray zone. But again, the top priority here should be the data.
Julie Conroy:
Great. And, next slide, David, in one minute, Andre, for you to bring us home here.
André Ferraz:
All right. One quick comment here on how location can help. One of the things we've seen in markets where real time payments have become widespread was the growth of the use of location as a signal for fraud prevention. For example, last year, we even saw Apple Pay starting to enforce the use of location for every user for fraud prevention purposes.
And the same has been happening in other countries. For example, Mexico has recently passed a law in which every FI has to collect location from their users, et cetera. And I wanted to come and hear about some of the use cases, right? So, first of all, location can help you bind the device to the identity in a continuous fashion.
So, what's interesting about this is you can use that to detect new accounts very effectively, right? So, if one account was created, everything looks good, but suddenly the address associated with that account no longer matches the behavior of the device that is accessing that account. It is most likely to be a new account, right?
Either the user has moved and didn't notify the FI or that's a new account. Second thing, which is interesting, is that we see in our network that over 95 percent of the real time transactions occur from places where the user goes very frequently, like your home, your office, et cetera. So, understanding that can help you both provide the frictionless experience to the good users, but also detect suspicious activity more effectively with real time information, right?
Basically, those are just two examples here of how location has been used by FIs. And I believe that's probably going to be one of the new areas of investment for the FIs as we move into this space.
Julie Conroy:
Awesome. So, David, any last comments for us?
David Nesbitt:
Yeah, thanks all. Thanks to our three presenters and to everyone who attended and contributed questions. Like I said, we'll be sending out the recording shortly. If you have any last questions that you didn't get to ask, feel free to respond to any of the reminder emails you got from info@incognia.com. We'll make sure to get answers to those, but thanks for enjoying, for joining. Please share the recording with your colleagues if you benefited from it and hope you have a wonderful day. Thanks everybody.