- Blog
- Playing the Numbers Game: Why Fraudsters Can Afford A 99% Failure Rate
Playing the Numbers Game: Why Fraudsters Can Afford A 99% Failure Rate
Fraudsters are willing to fail thousands of times if they can succeed dozens, and that’s because it doesn’t cost them much to try. Using tools like multi-accounting, generative AI, and bots to expand their reach, fraudsters can try as many times as it takes before they find a vulnerable user or platform. In this post, we explore how this numbers game works for fraudsters and what fraud fighters can do about it.
Subscribe to Incognia’s content
For those who prefer listening over reading, we've provided an audio transcription player below, allowing you to enjoy this post through your speakers or headphones.
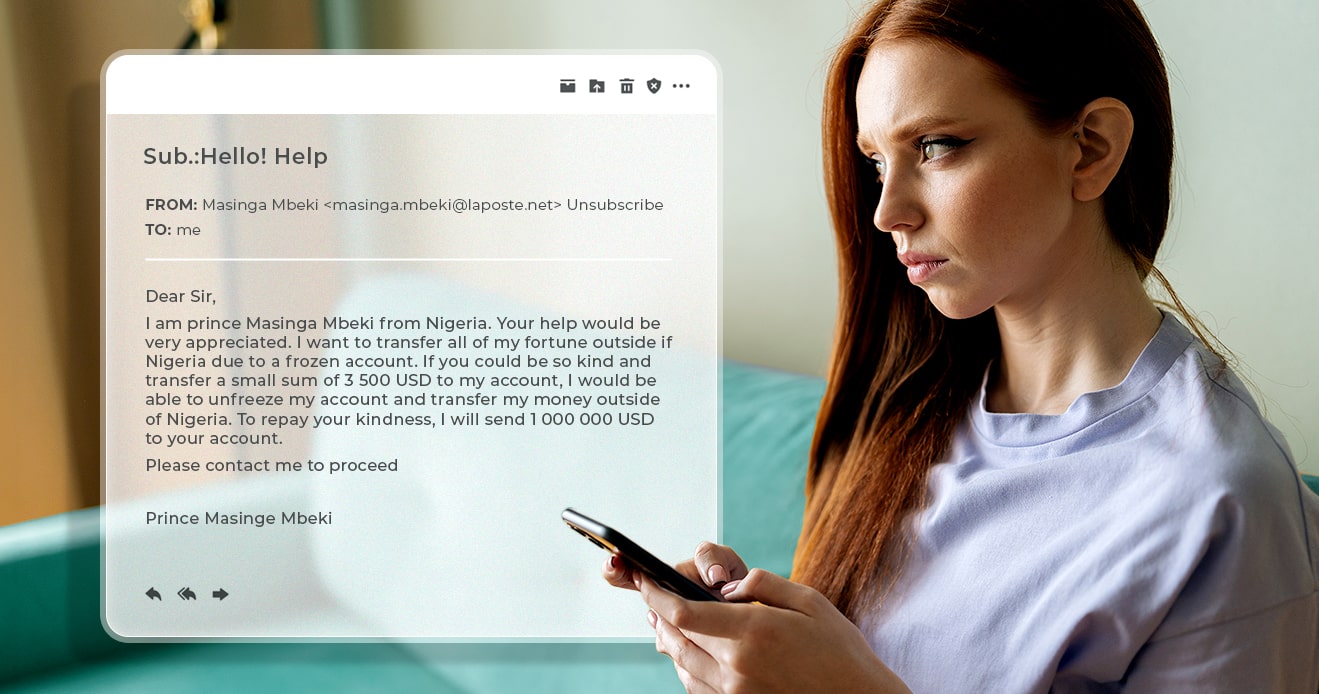
The transparency of some scams and fraud schemes is so notorious these days that it's common to joke about the ridiculousness of a mysterious inheritance promised by a Nigerian prince over email, or about a poorly-written phishing text. “Seems legit, huh?” We might laugh before carrying on with our day.
Most users have learned to treat the Internet with a healthy level of skepticism. They know not to click strange links, not to give passwords out over phone or email, and that if something sounds too good to be true, it probably is. But most users aren't all users, and that gap is where fraudsters make their living—to the tune of $12.5 billion consumer losses in 2023.
Fraudsters understand that if they can reach enough people, they’ll eventually find someone vulnerable to their tactics. Likewise, if they can create enough accounts to abuse a platform, it won’t matter how many others get banned for policy violations. As long as fraudsters have the power to push their numbers as high as they want, at least some level of success is inevitable.
Multi-accounting, bots, and GenAI let fraudsters cast a wide net
The more people they can reach and accounts they can control, the better fraudsters will do. If they can optimize their multi-accounting to make it as cheap and quick as possible, too, that’s another layer that makes it easier for them to push their ROI—at platforms’ and users’ expenses. In a webinar called “Scam Stopper: Buyer/Seller Verification in P2P Marketplaces,” Arūnas Umbrasas, the Trust & Safety Data Science Director at Vinted, described the way fraudsters approach high volume attacks with multi-accounting:
“But the common pattern here for the bad actors is that they require a lot of accounts to do their bidding. The playbook is basically I control many, many, and sometimes it can be hundreds or thousands of accounts on the platform. I engage in malicious activity with all of them sequentially or at the same time, but only a relatively limited proportion will be successful and make a profit for the attacker. So what that means is that they have to make the account creation process really cost effective, but have the accounts be reputable enough that they don't just get banned immediately.”
Any scheme can be scaled using multi-accounting. Dropshipping, counterfeiting, fake listings, social engineering, policy abuse (taking advantage of good-faith policies on the platform side to make a profit), refund abuse, and phishing are just some of the use cases for a fraudster with hundreds of user accounts at their disposal.
Bots and generative AI are some additional technologies that can help fraudsters expand their operations by saving them time and energy. Bot accounts can be used to message marketplace users en masse and alert the fraudsters when someone “bites,” and generative AI makes it easier than ever for fraudsters to fabricate PII and craft hundreds of phishing and social engineering messages.
It won’t work on everyone, but it doesn’t have to
Like Arūnas pointed out, fraudsters will likely only be successful in a relatively small proportion of their attempts. Pushing the number of the attempts as high as possible is how they make their schemes a viable way to make money.
Think about it like this: if a fraudster only has a 1% success rate with phishing people for their banking credentials over Instagram, an attack vector Incognia has seen before, that might not seem high enough to be worth the effort. But if that same fraudster can manage to reach 100,000 users with bots, multi-accounting, generative AI, and other tools, then that’s 1,000 people whose bank accounts could be compromised.
Fraudsters don’t have to do this work manually, which means that they can push the numbers so far that their success is statistically inevitable.
Persistent device intelligence cuts fraudsters down at the root
If account creation is the lever fraudsters pull to make this kind of numbers gaming possible, how do we address account creation at the root? How do we stop fraudsters from making enough accounts to make their operations financially viable?
User verification can help by targeting friction towards fraudsters through step-up verification for the riskiest devices and new signups. If fraudsters have to invest more resources into passing verification, i.e., finding synthetic or stolen identity information, using aged email accounts, acquiring new phone numbers, etc., that might be enough to discourage them from setting up shop on that platform because it cuts into their profit margins. However, it isn’t a foolproof way to cut multi-accounting off at the root, only make it more difficult.
One of the best ways to limit multi-accounting is to have a reliable way to re-identify users across devices, accounts, and app installations.
If you can say with confidence that someone trying to create a new account is a user you’ve seen before, you can block that account creation and cut off a high volume attack before it can even start.
Traditional device intelligence can be spoofed by factory resets and device parameter manipulation, but combining device intelligence with other signals lets us identify devices even beyond obfuscation attempts.
For example, Incognia uses location as a secondary signal. If we can see that an extremely high concentration of accounts exist in one particular location, that’s a good indication that someone there is using multi-accounting. Likewise, if someone tries to wipe their device and rejoin, we can look to their location to confirm that it’s still the same device, despite the fraudster’s attempt to hide that fact.
Fraudsters are willing to fail 99 times if it means they can succeed once, because the price of each attempt is so low that they can attempt an abuse as many times as they want. Smart friction and reliable device intelligence can help stop fraudsters at the root by limiting how many times they can try before the costs outweigh the rewards.