Recent posts
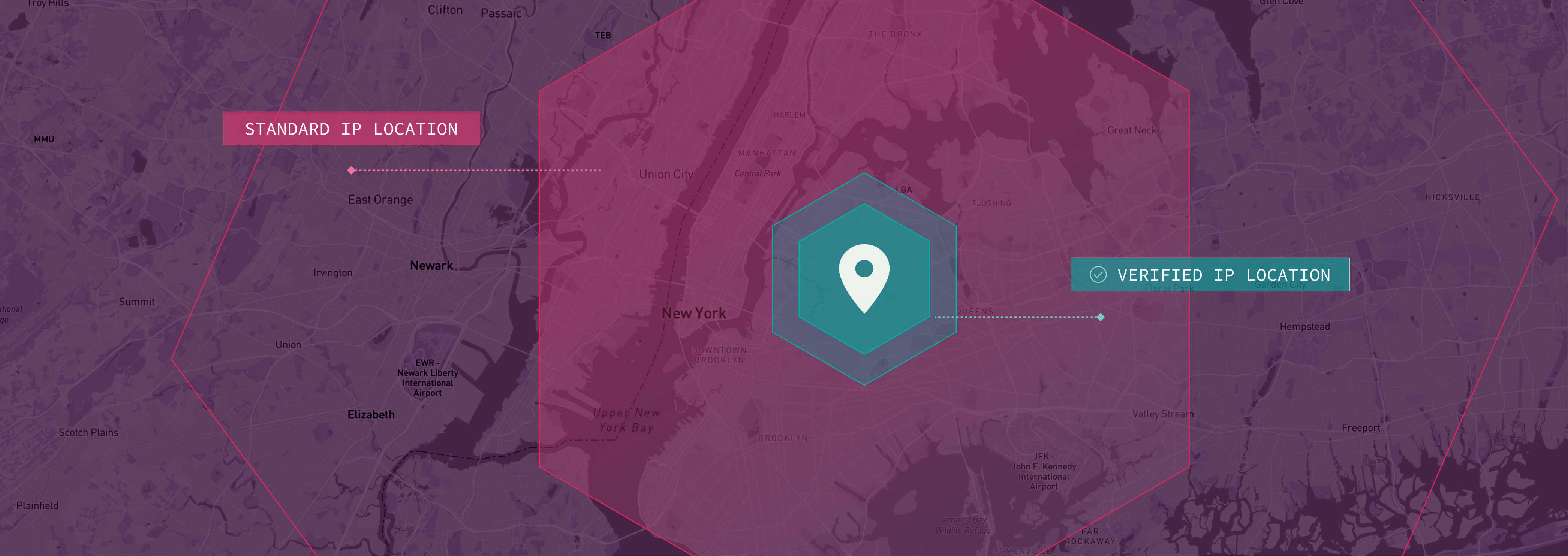
Verified IP Location: Know Where Your Web Traffic is Actually Coming From
Enhance security with Incognia's Cross Device...

Cross Device Authentication: Verify the Right Person in the Right Place
Enhance security with Incognia's Cross Device...
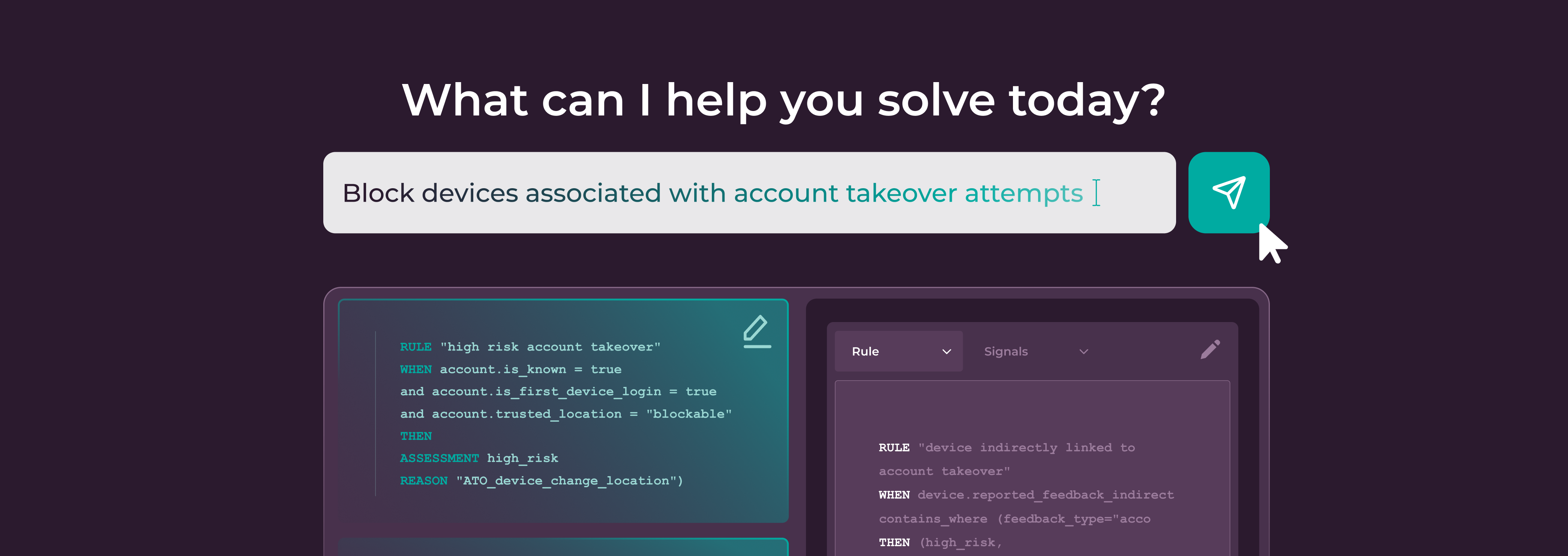
AI Rule Builder: The Next Innovation in How Fraud Rules Get Built
Discover how Incognia's AI Rule Builder revolutionizes...
Why Incognia’s AI-Powered Browser ID is the Next Standard for Web Identity
Discover how Incognia's AI-powered Browser ID redefines web...

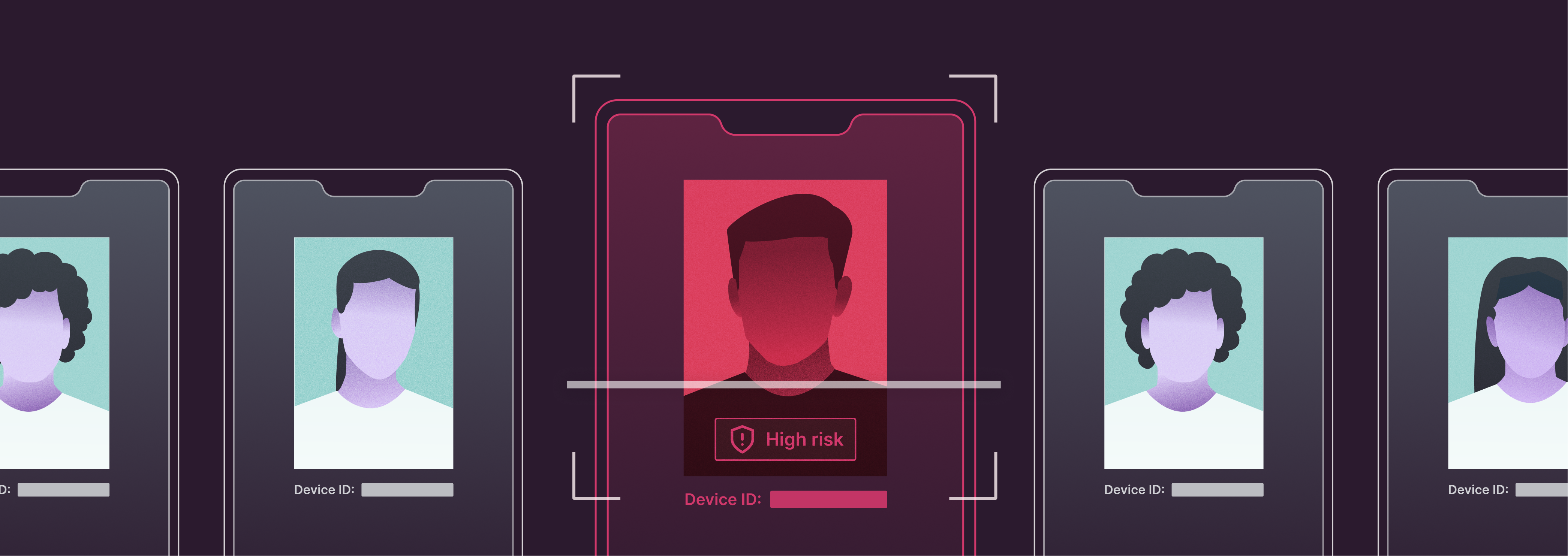
Incognia’s Network Graph: Persistent Device ID for Faster Fraud Investigations
Persistent and tamper-resistant device IDs in Incognia's...

How Marketplaces Can Outsmart Seller Fraud in 2026
Discover how to combat sophisticated seller fraud in 2026...

Episode 4: How Rapido Balances Driver Supply with Fighting Fraud
Learn how Rapido balances driver supply and fraud...

How App Cloners are Becoming a One-Stop-Shop for Fraudsters
Take a deep dive into the rise of app cloners and what...

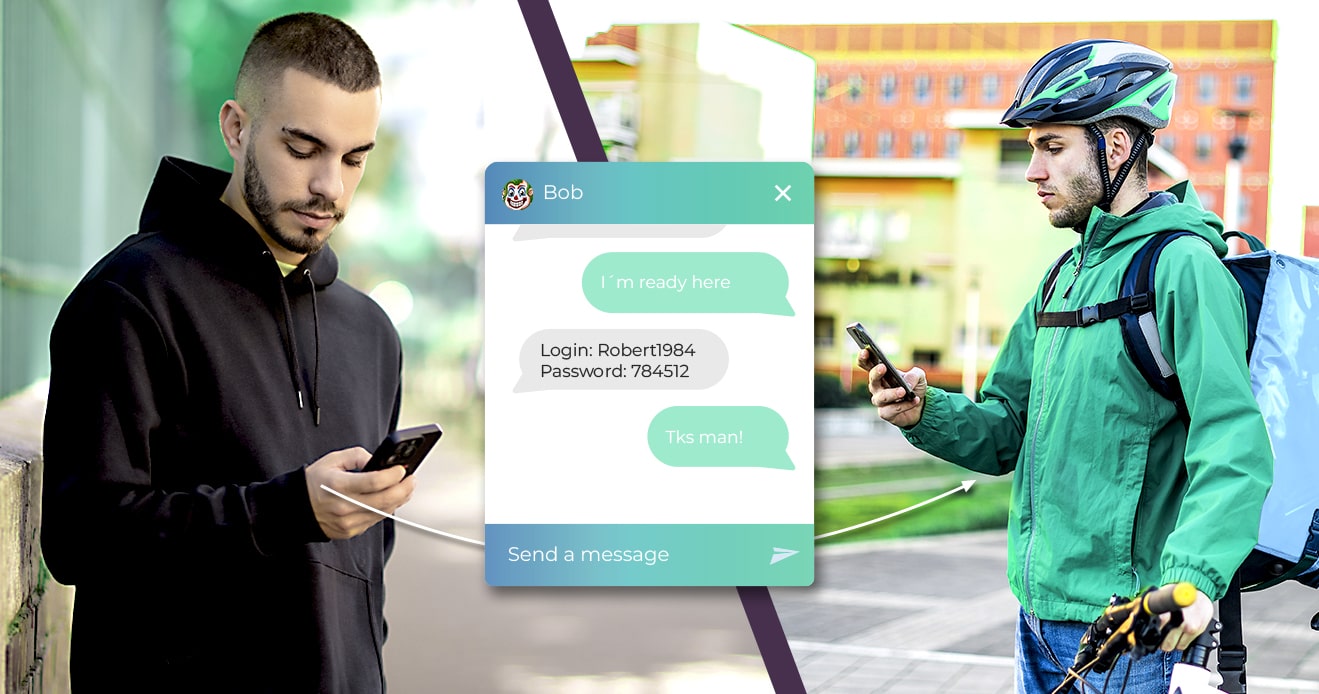
Collusion on Gig Platforms: Trends, Types, and Solutions
Discover how gig platforms can detect and prevent collusion...

The Gig Economy Fraud Trends to Know for 2026
Stay informed about gig economy fraud trends to know for...
5 Ways Gig Economy Platforms Can Strengthen Fraud Prevention in 2026
Learn 5 effective ways delivery and ride sharing platforms...

Episode 3: Fighting Back Against Promo Abuse
Learn how gig economy platforms combat promo abuse, detect...

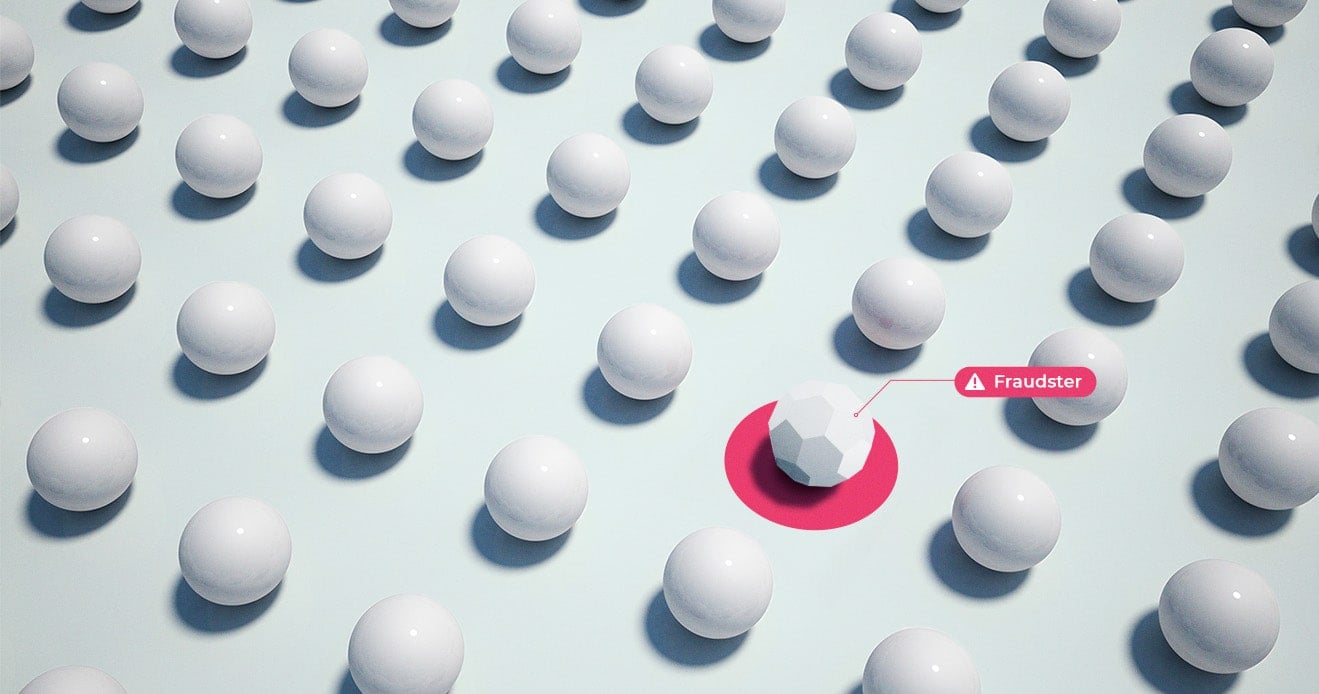
Ban Evasion: How Platforms Can Shut Out Repeat Offenders
Struggling with ban evasion on your platform? Learn how you...

Episode 2: Building Trust Scores to Fight Fraud and Reward Good Users
Learn how how Rebel Foods uses data-driven trust scores to...

Episode 1: Fighting Courier Fraud in Cash-on-Delivery Markets
Explore COD’s hidden risks in emerging markets—from courier...

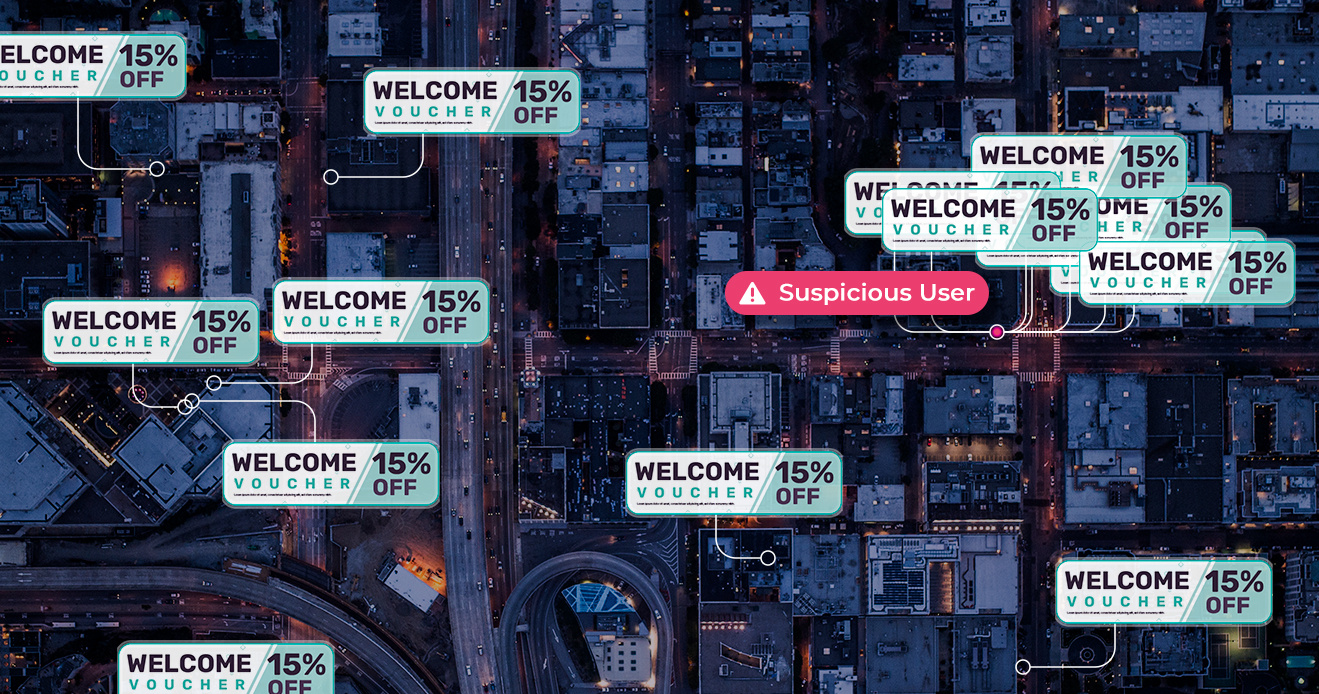
Promo Abuse: The Silent Fraud Hiding Behind Your Best Campaigns
Learn how to detect and prevent promo abuse in the gig...
Understanding 3 Different Types of Collusion on Food Delivery Platforms
Explore collusion on food delivery industry. Learn about...

How to Make the Case for Fraud Prevention With Different Departments
Learn how to communicate the value of fraud prevention more...
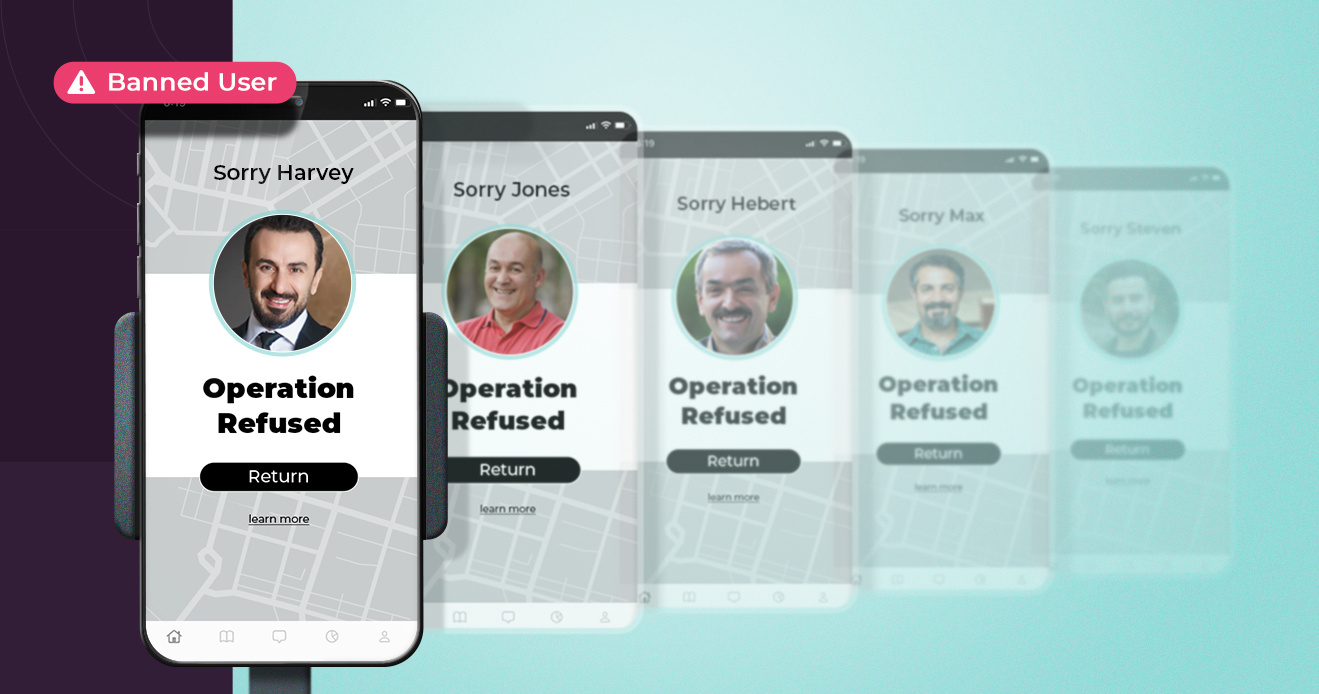
3 Ways Multi-Sided Platforms are Defeating Ban Evasion
Explore how multi-sided marketplace platforms are tackling...
Death by 1,000 Cuts: Why Even “Small-Time” Fraud Matters on Food Delivery Apps
Dive into the impacts of seemingly small-scale fraud on...

ELF: The Persistent Signal Fraudsters Can't Erase
Learn about the threat of recurring fraud and the...

Why Solving Multi-Accounting Is Worth Your While
Learn about the return-on-investment potential of tackling...
New Account Fraud: Are You Missing This Critical Ride-Hailing Fraud Problem?
Learn about the impact new account fraud has on ride...

Fraud Prevention Doesn’t Kill Growth, Multi-Accounting Does
Fraud prevention is sometimes seen as hurting growth, but...
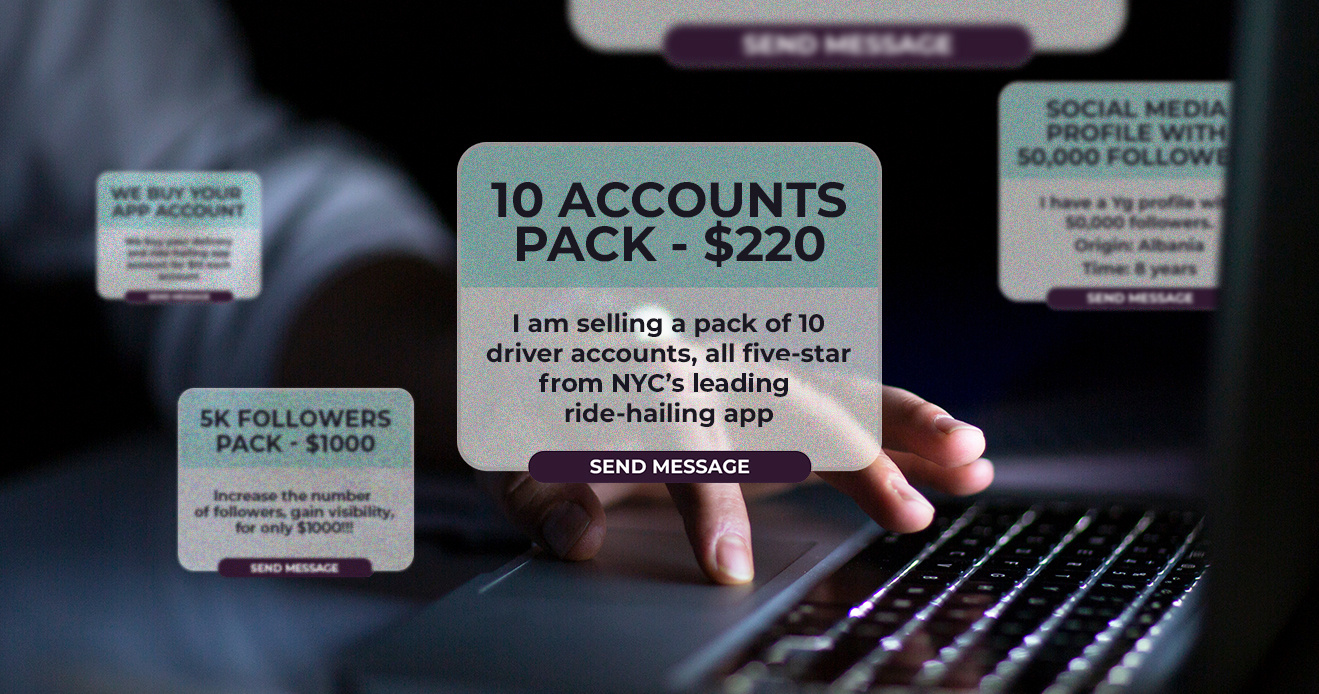
Fraud For Sale: Multi-accounting and Fraud on Gig Economy Apps
Take an insider look at the fraud-as-a-service tools used...
The Fraud-as-a-Service Economy: How Fraudsters Make a Living Attacking Gig Economy Platforms
Learn about the underground economy fueling fraud on gig...

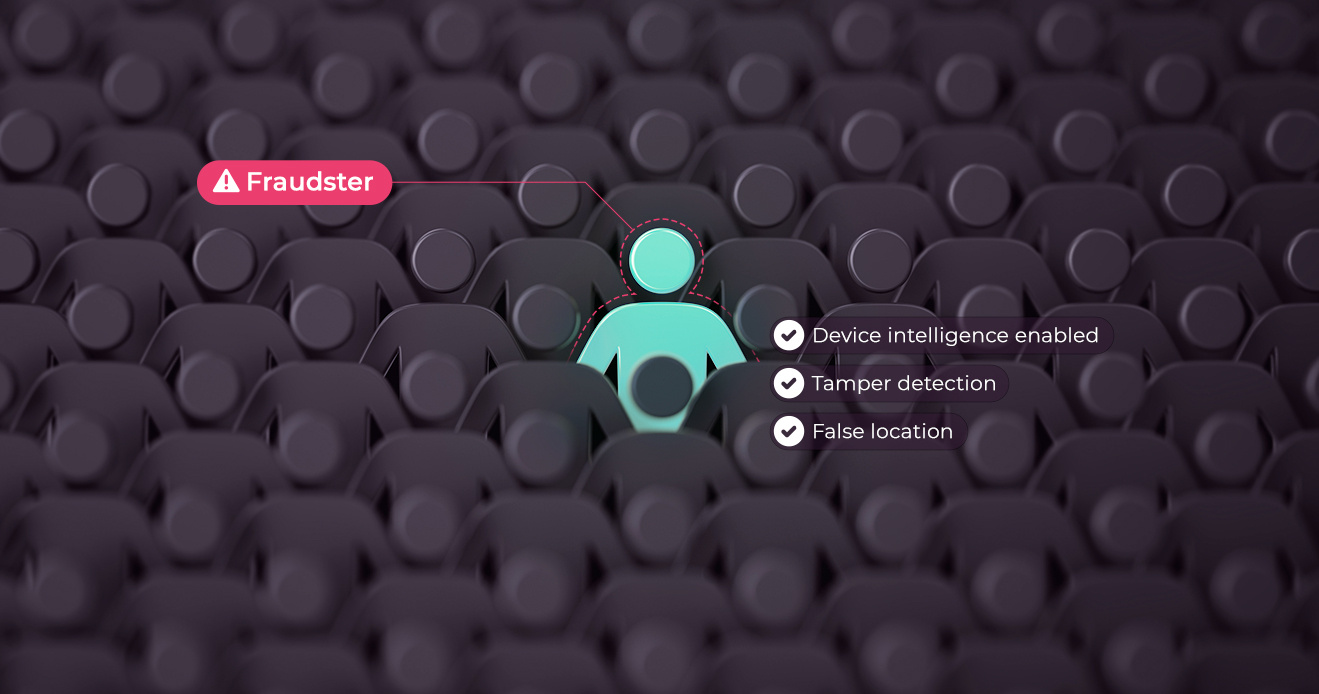
The Fraudster's Playbook: How Fraudsters Defraud Your Platform
Learn about the step-by-step process fraudsters take to...

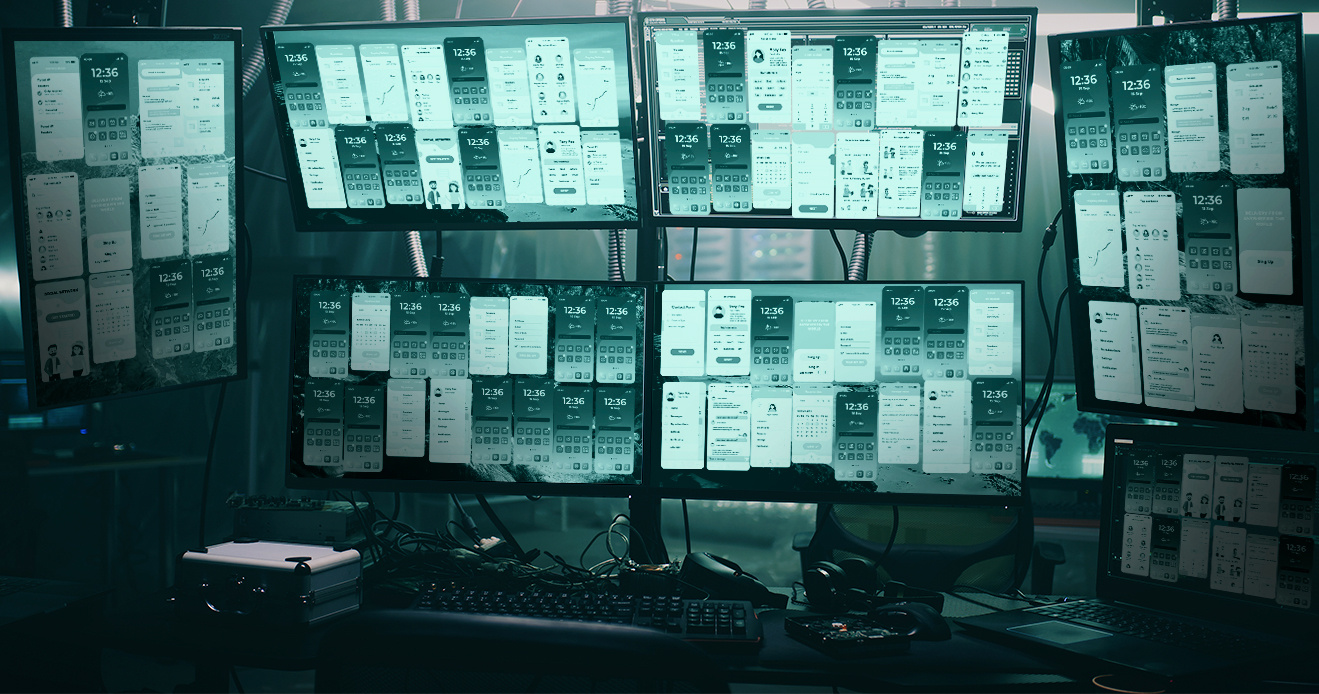
Device ID Obfuscation: How Fraudsters Make 1 Device Look Like 300
Learn about device ID obfuscation and how bad actors stop...

3 Fraud-as-a-Service Tools Every Food Delivery Platform Should Know About
Learn about the Fraud-as-a-Service tools impacting food...

You Are Who People Say You Are: Understanding the Reputational Impact of Courier Scams
Explore the real impact that courier scams can have on a...
Stop Ban Evasion Even When Fraudsters Get Creative With Obfuscation
Prevent ban evasion by learning about fraudsters' tactics...

Why Browser Intelligence Has to Evolve to Support Financial Institutions & Online Marketplaces
Learn about threats facing online financial institutions...

The Ban Evasion Toolkit: Techniques Fraudsters Use to Evade Bans
Learn how fraudsters evade bans and discover effective...
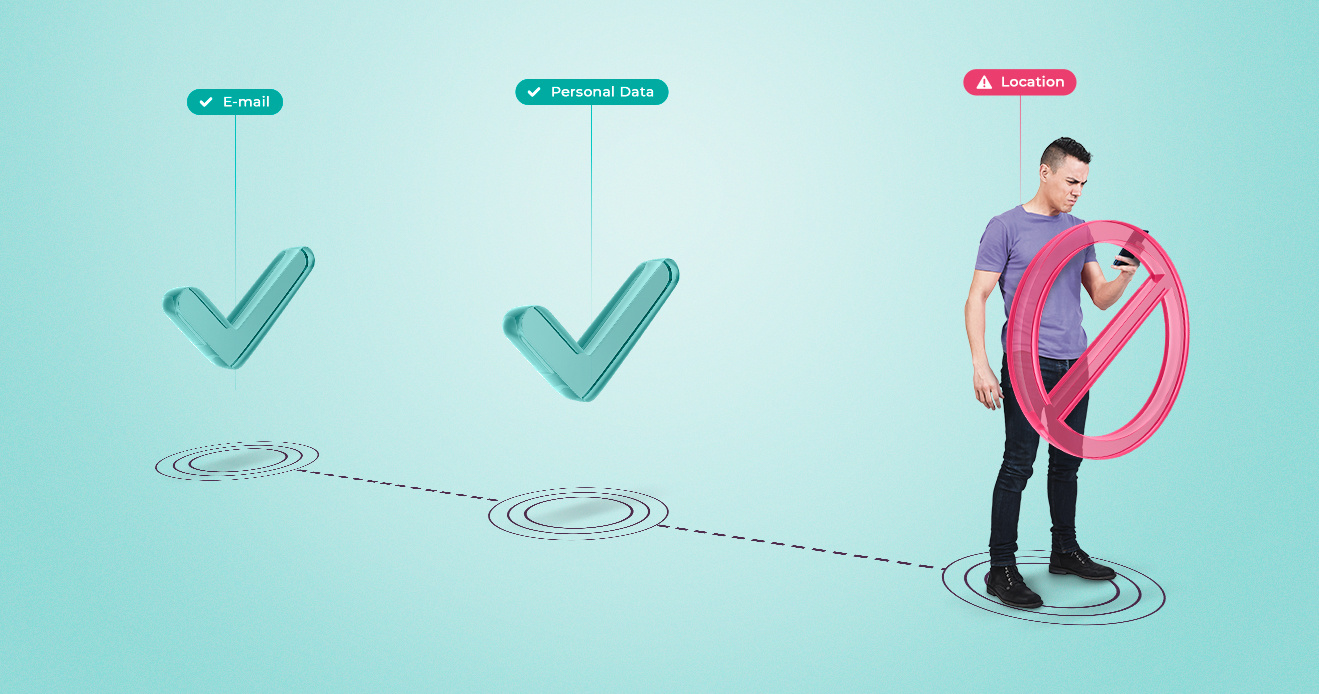
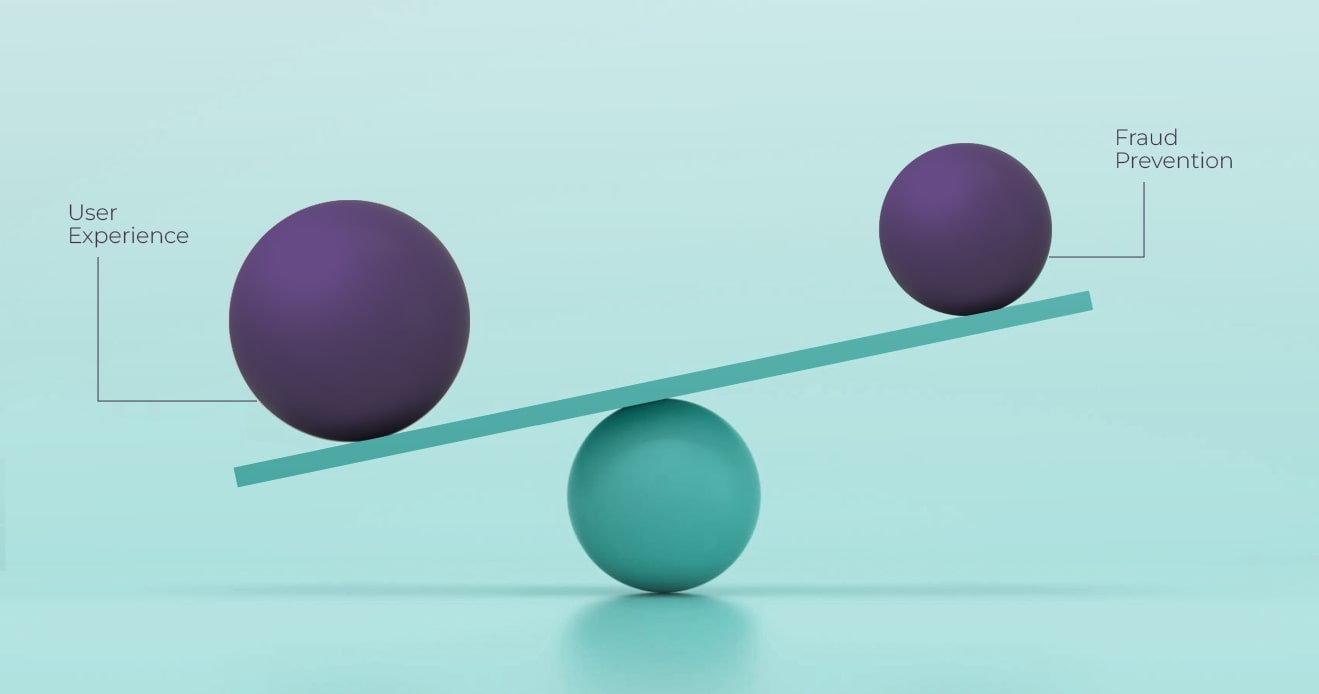
Managing Friction and User Verification: Remembering the User’s Perspective
Explore how effective communication and user collaboration...

Smart Friction: Targeting Your Friction Toward Fraudsters, Not Good Users
Explore how smart friction and passive signals can enhance...
Playing the Numbers Game: Why Fraudsters Can Afford A 99% Failure Rate
Explore how multi-accounting enables fraud, and how...

The 4 Promotion Campaign Mistakes Fraudsters Feast On
Learn key mistakes to avoid in your promo campaigns to...

Balancing Growth Tactics With Fraud Prevention: How to Protect Promo Campaigns From Abuse
Learn key strategies to protect your promotional campaigns...
How Organized Fraudsters Run Their Operations Like a Business (And How Fraud Fighters Can Use That Against Them)
Explore how organized fraudsters exploit promotions and how...
Churn or Burn? Telling the Difference Between Low Retention and Promo Abuse
Learn how to tackle promo abuse with strategies on user...

Bad Actors at Scale: The Real Cost of Fraud & Policy Abuse
Explore how promo abuse at scale impacts businesses and the...
How Fraudsters Find Quick Workarounds For Fraud Prevention Tools (And How to Stay Ahead)
Learn how fraudsters outfox fraud prevention’s industry...
Communicating the Value of Fraud Prevention to Executives
Learn how to communicate the value of fraud prevention to...

How to Overcome Fraudsters’ Speed Advantage and Stop Playing Catch Up
Discover how fraud prevention teams can overcome speed...
Data Quality: The Missing Piece of the Build vs. Buy Fraud Prevention Debate
Explore the build vs. buy dilemma in fraud prevention....

Fraud on Restaurant Reservation Apps: How Bad Actors Are Ruining Dinner Plans & Stealing a Seat at the Table
Explore how bad actors are exploiting digital reservations,...

Having Your Delivery and Eating it Too: Managing Food Delivery Fraud Without Causing Driver Churn
Explore how food delivery platforms balance fraud...
The Hidden Costs of Internal Fraud Prevention
Should I invest in a third-party fraud prevention solution,...

Unveiling the Hidden Threat: Tackling 'Off-line Rides' in Ride-Hailing Apps
Explore how offline rides impact ride-hailing platforms and...

Incognia: Strategic Expansion & Focus on Device and Location Data for Fraud Prevention
Learn about Incognia's $31M Series B funding round, our...

How & Why Driver Account Sharing Happens (And How Food Delivery Apps Can Prevent It)
Explore techniques to combat unauthorized account sharing...
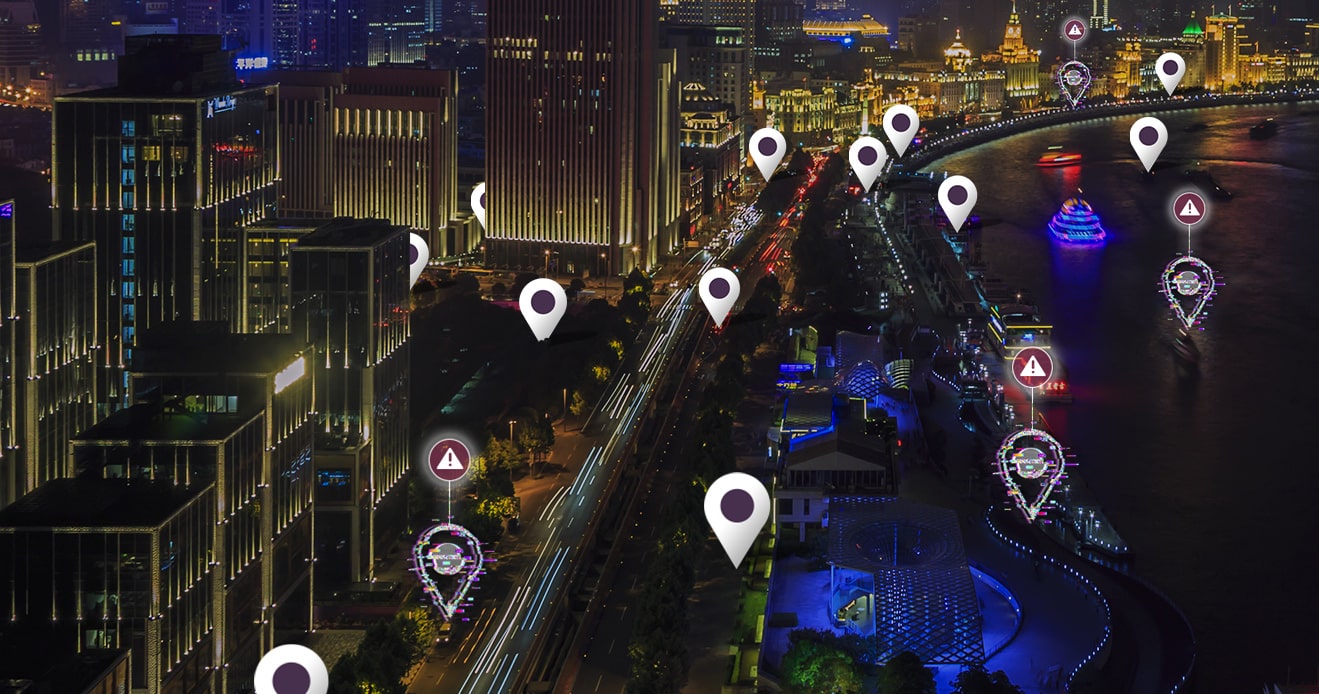
Exploring 3 Different Location Spoofing Methods Used By Fraudsters
Dive into the 3 different location spoofing methods...

The Importance and Challenges of Listing Verification for Online Marketplaces
Explore how to enhance listing verification in P2P...

How Fraud Prevention and Marketing Can Work Together Against Promo Abuse
Explore how promo abuse impacts your digital marketing...
What’s Mine is Yours? How Ban Evasion and Account Sharing Are Costing Food Delivery Apps Money
Discover how food delivery platforms can combat fraudsters'...
Using Location Data to Detect Mule Accounts
Explore strategies to detect mule accounts in real-time...

Reduce fraud losses, increase profits: how fraud prevention functions as a profit center
Discover how fraud prevention makes important impact on the...
Optimizing Your Fraud Prevention Stack
Learn how to build the ideal fraud prevention stack, and...
Real-Time Fraud Prevention in the Age of Faster Payments
Explore how real-time payment systems impact fraud...

Off-the-shelf device ID could be sabotaging your fraud prevention efforts
Explore the significance of device IDs in fraud prevention...
Fighting ATOs with next generation device recognition
Explore insights from industry experts on the role of...

Fraud in Draw Games: How to Prevent iLottery Fraud
Explore the prevalent types of iLottery fraud, from payment...
Identity verification is make-or-break for your platform's growth
Learn why identity is the cornerstone for trust & safety on...

Gambling Compliance: How to Add Extra Layer of Protection
Discover how multiple layers of security can ensure safer...

Detecting suspicious environments is a paradigm shift
Discover how detecting suspicious environments reveals new...

A Comprehensive Analysis of Device Intelligence Spoofing Techniques
Read to understand the evolution of device intelligence and...

Cutting Through the Noise: 2 generative AI threats to prepare for
Discover the two generative AI threats that fraud...
Using Seller Fraud Detection to Prevent Marketplace Scams
Discover how to detect risk signals and prevent potential...

5 Best Practices for Preventing Refund Fraud in Food Delivery
Safeguard the integrity of your food delivery service!...

Main policy violations & scams in food delivery apps
Are you a food or grocery delivery app? Find out what...

As device intelligence becomes more challenging new risk signals emerge
Bringing new behavioral signals to the market, and...
![Featured image for How to Reduce Bonus and Promo Code Abuse in Food Delivery [Guide] resource](https://www.incognia.com/hubfs/promo-code-abuse-in-food-devivery.jpg)
How to Reduce Bonus and Promo Code Abuse in Food Delivery [Guide]
Prevent promo code abuse in food delivery apps: Learn about...

The Shared Account Challenge: Best Practices for Securing Food Delivery Apps
Are you a food delivery app struggling to prevent...

Courier Scams: How Location Verification Can Uncover Them
Find out what scams couriers commit and how location...

Account creation fraud: How to detect multiple accounts in food delivery apps?
Protect your app's integrity and avoid revenue losses with...
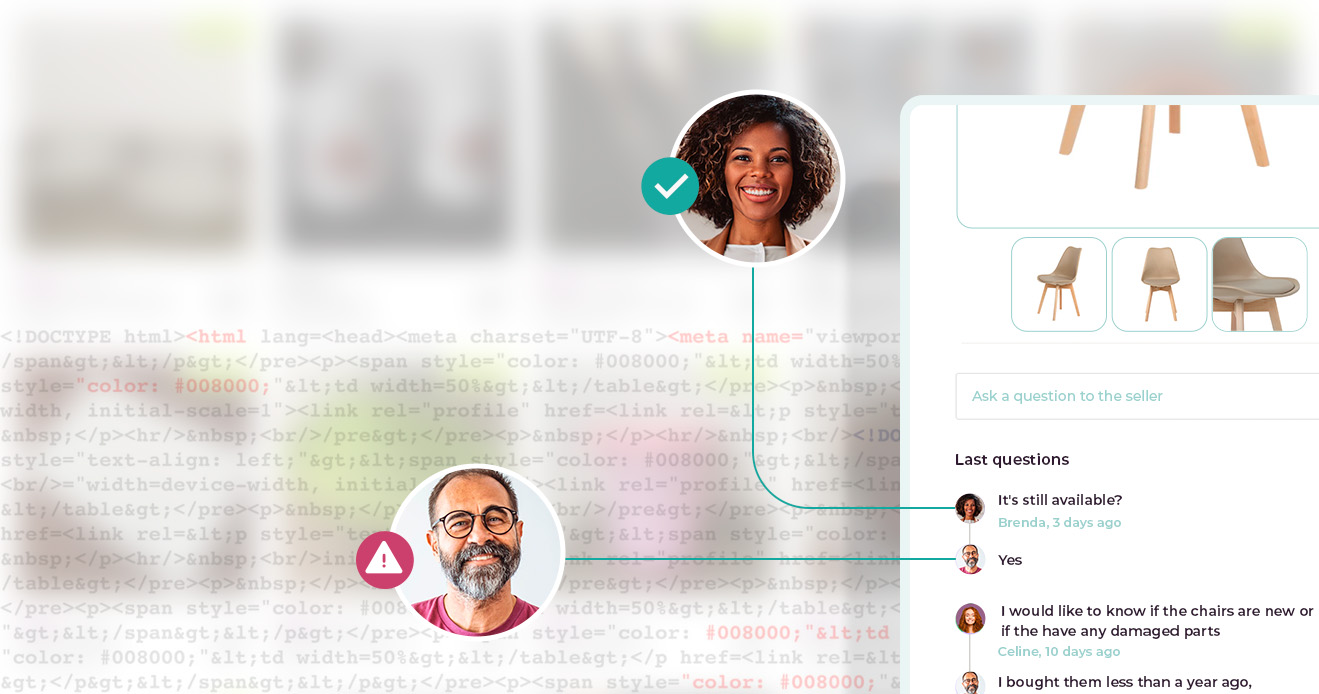
Why Online Identity Verification is Critical for Peer-to-Peer Marketplaces
Find out why online identity verification should be an...

The State of User Verification for Peer-to-peer Marketplaces
For online marketplaces, efficient user verification...

Machine Learning: How Incognia Data Makes the Difference
In this article, we take a closer look at how Machine...

The Fundamentals of Real-Time Address Verification
In this article, we take a closer look at the fundamentals...
How Delivery Platforms Can Detect Coupon Scams
Learn how to detect promotion and coupon scams to protect...

Top 5 Most Common Address Verification Software
Find out which five types of address verification software...

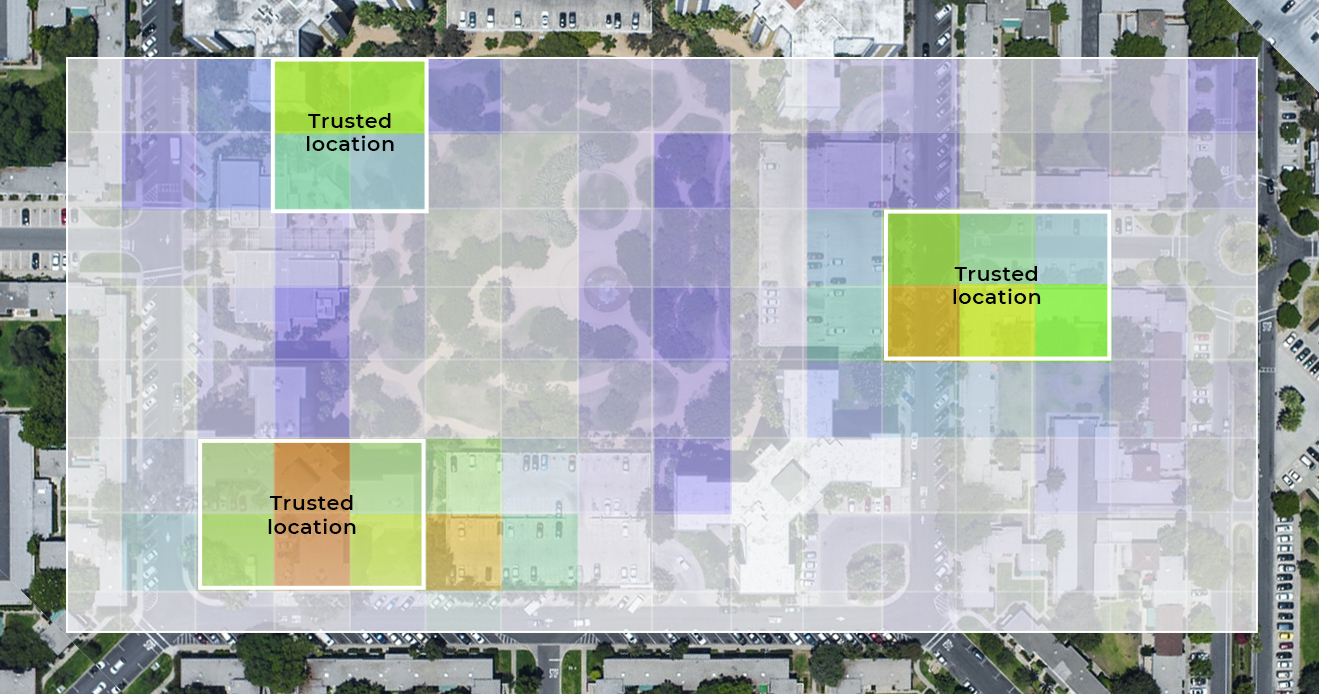
The Science Behind Incognia's Location Identity
From academic research to a powerful digital identity...

Who is faking location?
Location spoofing poses a threat to apps that rely on...
Fraud farms - Identifying where fraudsters are
Fraud farms are massive operations wherein fraudsters use...
Spoofing-resistant location data - the missing piece to addressing digital trust and safety
Location data is essential for digital trust and safety,...
![Featured image for Geolocation [An updated definition for identity, authentication, and fraud prevention] resource](https://www.incognia.com/hubfs/Geolocation%20-%20An%20updated%20definition%20for%20identity%2c%20authentication%2c%20and%20fraud%20prevention_.jpg)
Geolocation [An updated definition for identity, authentication, and fraud prevention]
The definition of what geolocation is, and what it can do...

How to block users playing outside of licensed jurisdictions
Online gambling is regulated, limiting individuals to...

Fraud farms take advantage of location spoofing to swindle mobile gaming apps
With fraud farms, fraudsters are able to mechanize and...
Why is device intelligence useless when fintech apps need it most?
Device intelligence will not recognize the login of a new...

Why Incognia when considering behavioral biometrics
Location behavior offers a compelling authentication signal...

Why OTPs Shouldn't Be Part of a Passwordless Strategy
A one time password (OTP) is a password that lasts for just...

It's Time to Stop Blaming the User
Social engineering is becoming increasingly sophisticated...

What is zero-factor authentication?
Companies are looking to adopt passwordless authentication....
![Featured image for Fintech Mobile App Friction Ranking [Login Authentication] resource](https://www.incognia.com/hubfs/featured-image-blog-mobile-app-friction-report-v2.jpg)
Fintech Mobile App Friction Ranking [Login Authentication]
Incognia Mobile App Study ranks Klover and eToro winners...

Five Ways Fraudsters Spoof Location
Location spoofing is now a standard technique used by...
How should location fit into a risk based authentication strategy?
How to implement frictionless risk based authentication...
Account Takeover Prevention Using Location Behavior
Strong Account Takeover Prevention could be achieved...
![Featured image for Prevent Mobile App Fraud [The Most Expensive Form of Identity Theft] resource](https://www.incognia.com/hubfs/%5BFEATURED%5DPreventing%20Mobile%20Application%20Fraud%20%5BThe%20Most%20Expensive%20Form%20of%20Identity%20Theft%5D.jpg)
Prevent Mobile App Fraud [The Most Expensive Form of Identity Theft]
Application fraud is a billion dollar problem for financial...
